window.open(url, name) is vulnerable to XSS with name collision · Issue #262 · w3c/html · GitHub
Por um escritor misterioso
Last updated 04 abril 2025
Xiaoran Wang (xiaoran@attacker-domain.com) This is a joint research with Travis Safford. window.open(url, name, [args]) makes it easy for websites accepting user supplied URLs to be vulnerable when attackers can cause a collision on the
🐛 Bug]: ERROR error sending request for url ( error trying to connect: invalid peer certificate contents: invalid peer certificate: UnknownIssuer · Issue #11406 · SeleniumHQ/selenium · GitHub
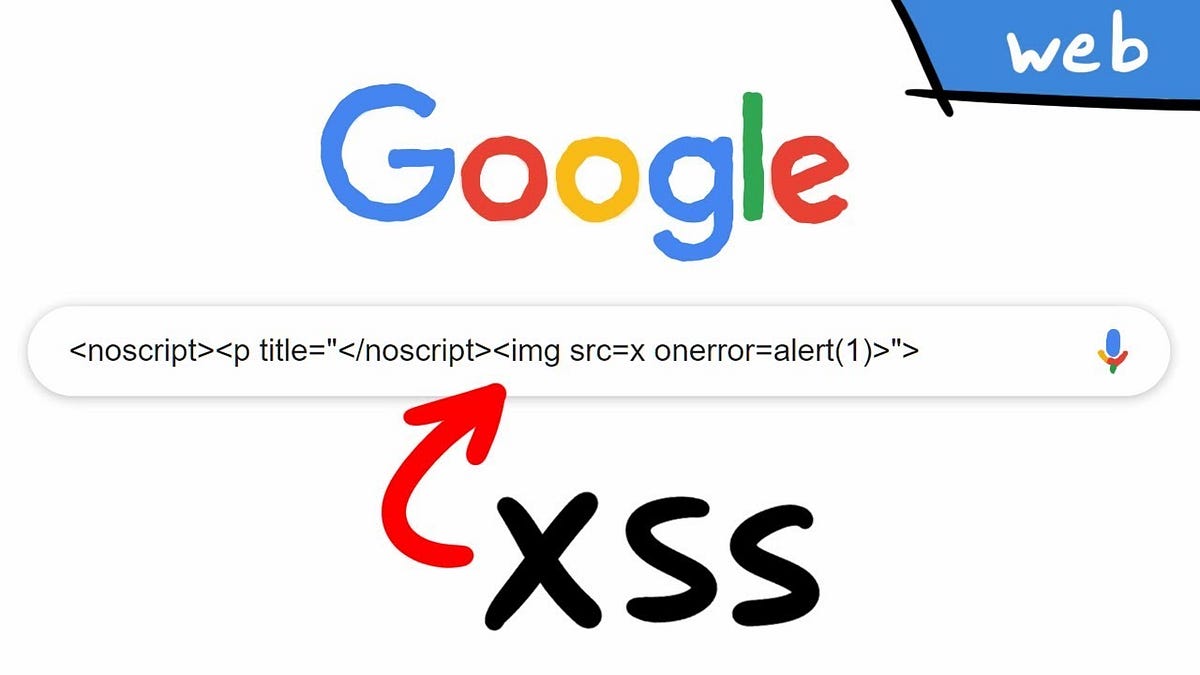
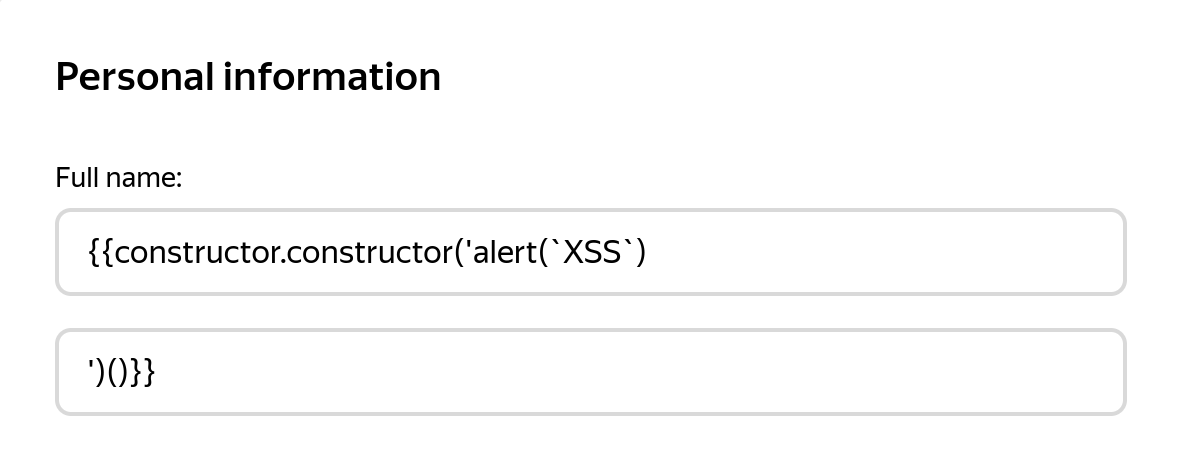
Cross Site Scripting ( XSS ) Vulnerability Payload List, by Ismail Tasdelen

Ckan, PDF, File Format
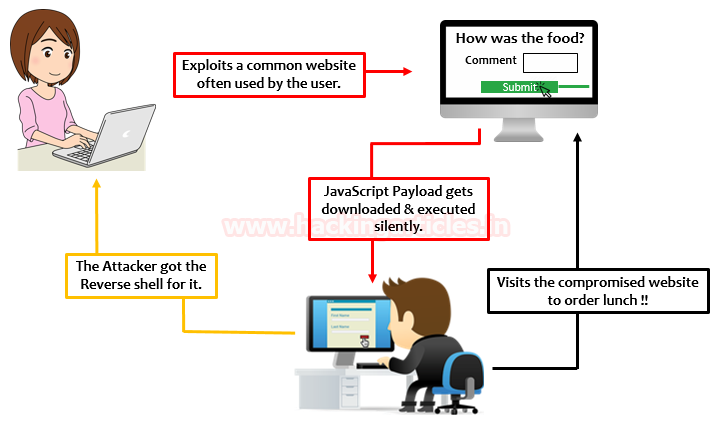
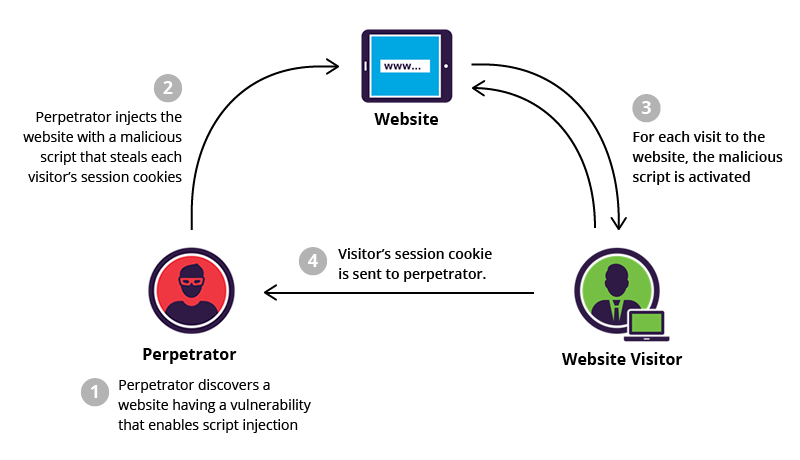
Cross-Site Scripting Exploitation - Hacking Articles
Missing required argument $name · Issue #294 · Smile-SA/elasticsuite · GitHub
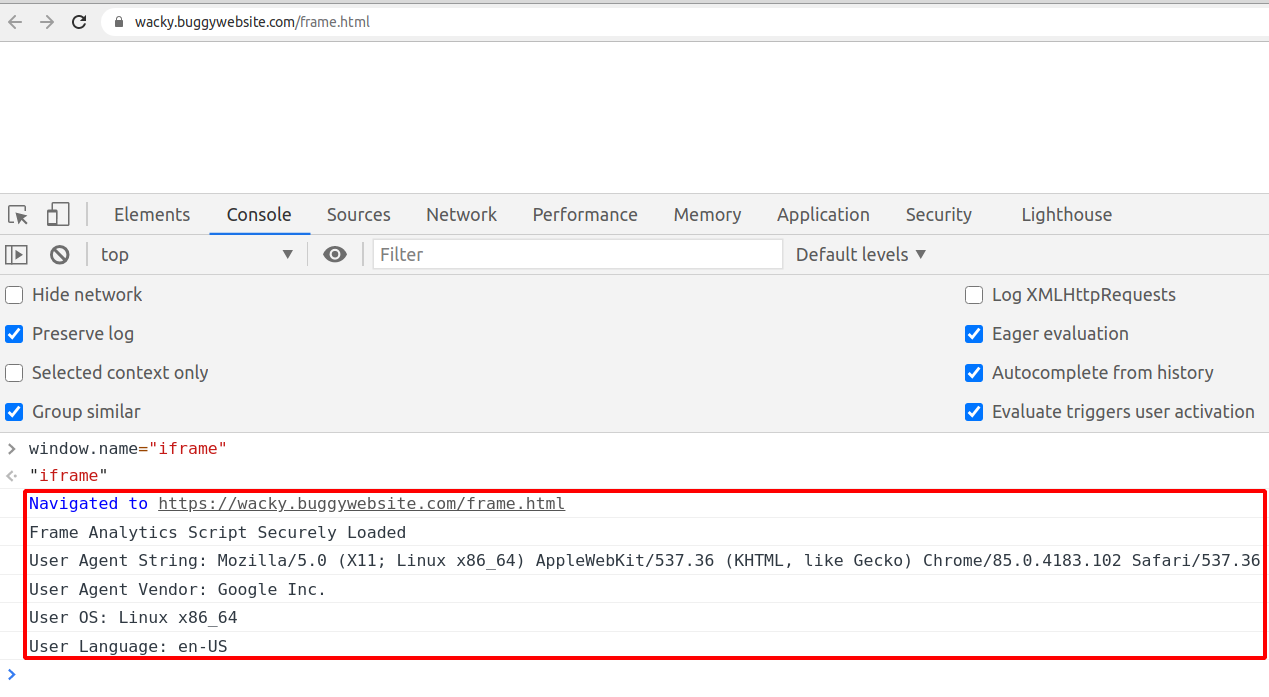
Wacky XSS challenge write-up. On November 4th BugPoc published a new…, by Daniel Santos

How We Found Another XSS in Google with Acunetix

Comprehensive Guide on Open Redirect - Hacking Articles

Security Weekly Podcast Network (Video)

eclipse - The type org.openqa.selenium.chrome.ChromeDriver is not accessible - Stack Overflow
Recomendado para você
-
 What is XSS, Stored Cross Site Scripting Example04 abril 2025
What is XSS, Stored Cross Site Scripting Example04 abril 2025 -
 An unusual way to find XSS injection in one minute04 abril 2025
An unusual way to find XSS injection in one minute04 abril 2025 -
 xsss – Tio Arthur04 abril 2025
xsss – Tio Arthur04 abril 2025 -
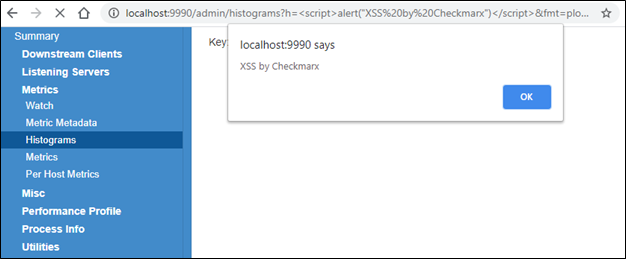 CVE-2020-35774: twitter-server XSS Vulnerability Discovered04 abril 2025
CVE-2020-35774: twitter-server XSS Vulnerability Discovered04 abril 2025 -
 AppFW XSS Was not getting detected04 abril 2025
AppFW XSS Was not getting detected04 abril 2025 -
 QUIKSILVER DEVILLE EQYEY03043 XSSS 54mm Sunglasses Shades Glasses Eyewear Italy - GGV Eyewear04 abril 2025
QUIKSILVER DEVILLE EQYEY03043 XSSS 54mm Sunglasses Shades Glasses Eyewear Italy - GGV Eyewear04 abril 2025 -
 XSS exploitation without using the
XSS exploitation without using the