PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 03 abril 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
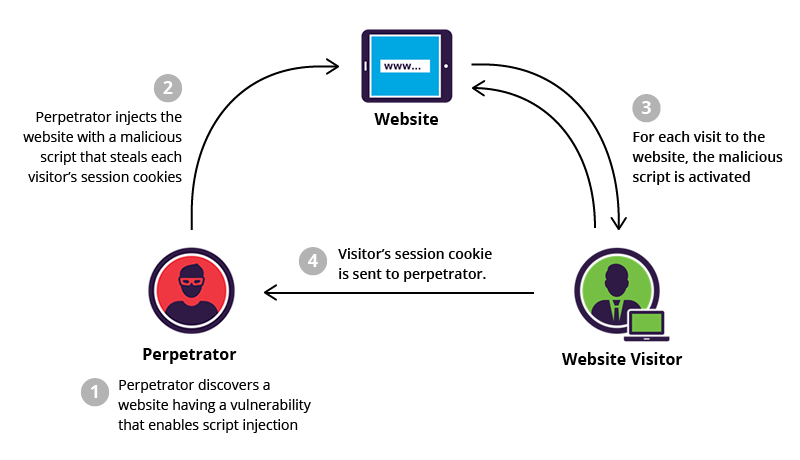
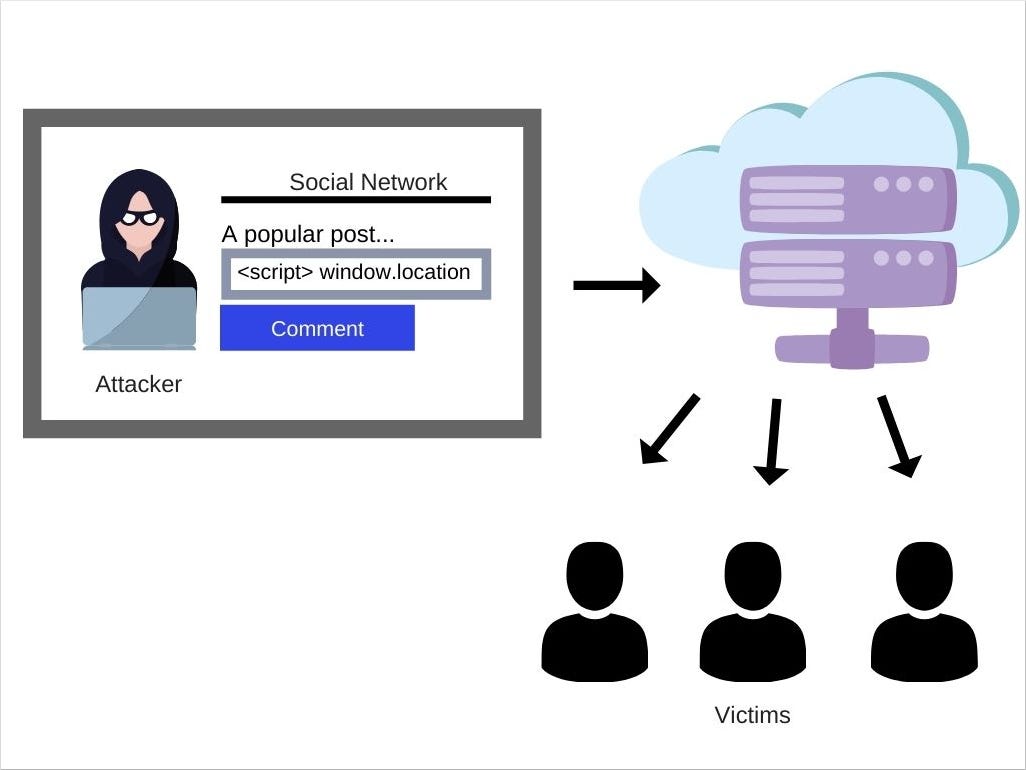
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://hackertarget.com/xss-simple-tutorial.png)
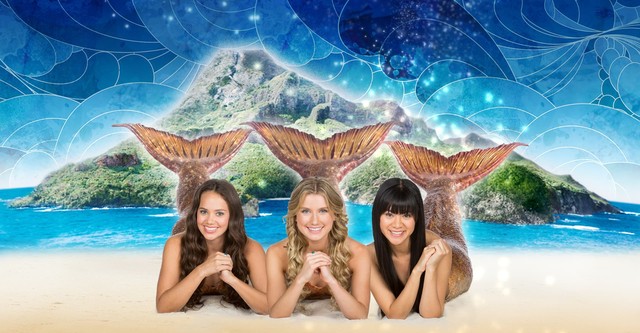
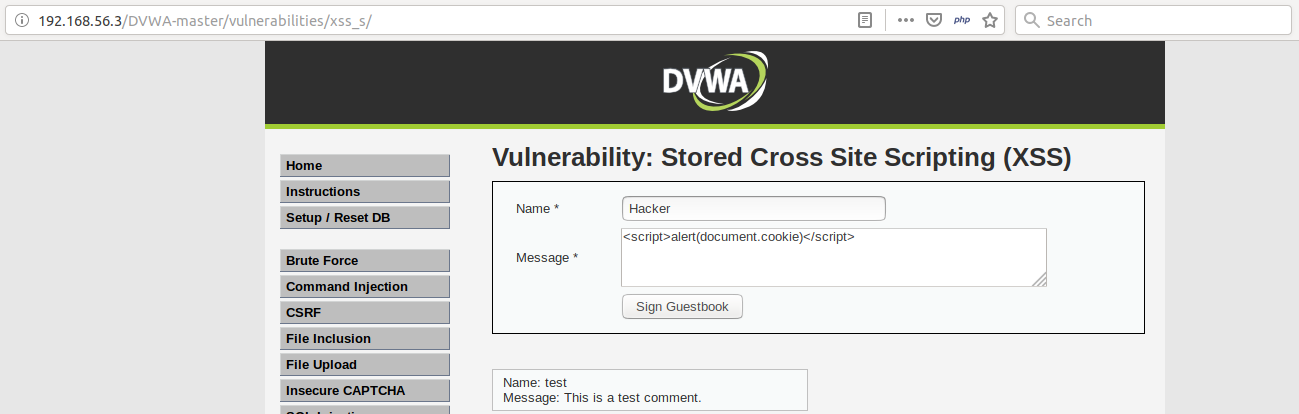
XSS Tutorial
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.researchgate.net/profile/Anny-Leema/publication/329683964/figure/fig4/AS:932153105846273@1599254027775/Analysis-of-various-services-in-Anti-XSS_Q320.jpg)
PDF) Eradicating cross site scripting attack for a secure web access
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://blog.netwrix.com/wp-content/uploads/2018/05/CA_cyberattacks_xssattack.png)
The 12 Most Common Types of Cybersecurity Attacks Today
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1007%2Fs11036-022-02052-z/MediaObjects/11036_2022_2052_Fig3_HTML.png)
Defining Cross-Site Scripting Attack Resilience Guidelines Based on BeEF Framework Simulation
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Figure4-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x10.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1038%2Fs41598-023-35198-1/MediaObjects/41598_2023_35198_Fig1_HTML.png)
A holistic and proactive approach to forecasting cyber threats
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs10462-023-10433-3/MediaObjects/10462_2023_10433_Fig17_HTML.png)
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/ijcatr03101001-141111002535-conversion-gate01/85/study-of-crosssite-scripting-attacks-and-their-countermeasures-1-320.jpg?cb=1669878105)
Study of Cross-Site Scripting Attacks and Their Countermeasures
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x8.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://cdn.acunetix.com/wp_content/uploads/2010/09/sql_inj_xss.gif)
SQL Injection - MDN Web Docs Glossary: Definitions of Web-related terms
Recomendado para você
-
 What is XSS, Stored Cross Site Scripting Example03 abril 2025
What is XSS, Stored Cross Site Scripting Example03 abril 2025 -
What is cross-site scripting (XSS)?, Tutorial & examples03 abril 2025
-
 How JavaScript works: 5 types of XSS attacks + tips on preventing03 abril 2025
How JavaScript works: 5 types of XSS attacks + tips on preventing03 abril 2025 -
 SQL injection and cross-site scripting: The differences and attack03 abril 2025
SQL injection and cross-site scripting: The differences and attack03 abril 2025 -
 Cross Site Scripting vs SQL Injection03 abril 2025
Cross Site Scripting vs SQL Injection03 abril 2025 -
 What Is Cross Site Scripting and How to Avoid XSS Attacks?03 abril 2025
What Is Cross Site Scripting and How to Avoid XSS Attacks?03 abril 2025 -
The architecture of XSS attack03 abril 2025
-
 How DOM Based XSS Attacks work03 abril 2025
How DOM Based XSS Attacks work03 abril 2025 -
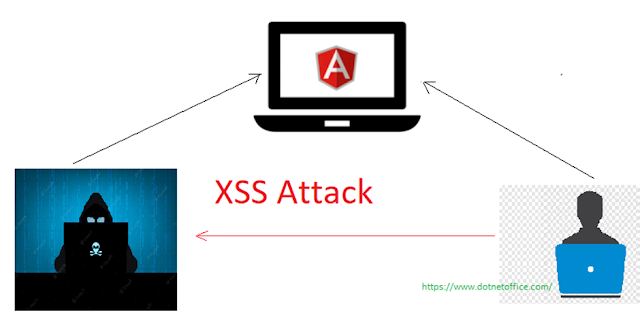 How To Prevent XSS(Cross Site Scripting) Attacks In Angular03 abril 2025
How To Prevent XSS(Cross Site Scripting) Attacks In Angular03 abril 2025 -
 Vulnérabilité XSS, ou injection de code indirecte à distance03 abril 2025
Vulnérabilité XSS, ou injection de code indirecte à distance03 abril 2025
você pode gostar
-
 Slayers Unleashed v.70 Stone Breathing Update Patch Notes - Try Hard Guides03 abril 2025
Slayers Unleashed v.70 Stone Breathing Update Patch Notes - Try Hard Guides03 abril 2025 -
 Classroom for Heroes Season 2: Release Date and Chances!03 abril 2025
Classroom for Heroes Season 2: Release Date and Chances!03 abril 2025 -
 All Item Drop Chance King Legacy03 abril 2025
All Item Drop Chance King Legacy03 abril 2025 -
Mako: Island of Secrets Season 2 - episodes streaming online03 abril 2025
-
 Siemens 6ED10561DA000BA0 LOGO! Memory Card03 abril 2025
Siemens 6ED10561DA000BA0 LOGO! Memory Card03 abril 2025 -
 Swansea City fixture release, Championship 2023-2403 abril 2025
Swansea City fixture release, Championship 2023-2403 abril 2025 -
 Call of Duty: Modern Warfare III review – exhilarating multiplayer03 abril 2025
Call of Duty: Modern Warfare III review – exhilarating multiplayer03 abril 2025 -
 Xbox: Brasil é 2° país que mais usa xCloud e PC Game Pass no mundo03 abril 2025
Xbox: Brasil é 2° país que mais usa xCloud e PC Game Pass no mundo03 abril 2025 -
 SCP 049 x reader 🍋🍋❤️ Various ! X Fem reader oneshots and03 abril 2025
SCP 049 x reader 🍋🍋❤️ Various ! X Fem reader oneshots and03 abril 2025 -
 TV Show My Little Pony: Pony Life HD Wallpaper03 abril 2025
TV Show My Little Pony: Pony Life HD Wallpaper03 abril 2025