Windows Command-Line Obfuscation
Por um escritor misterioso
Last updated 31 março 2025
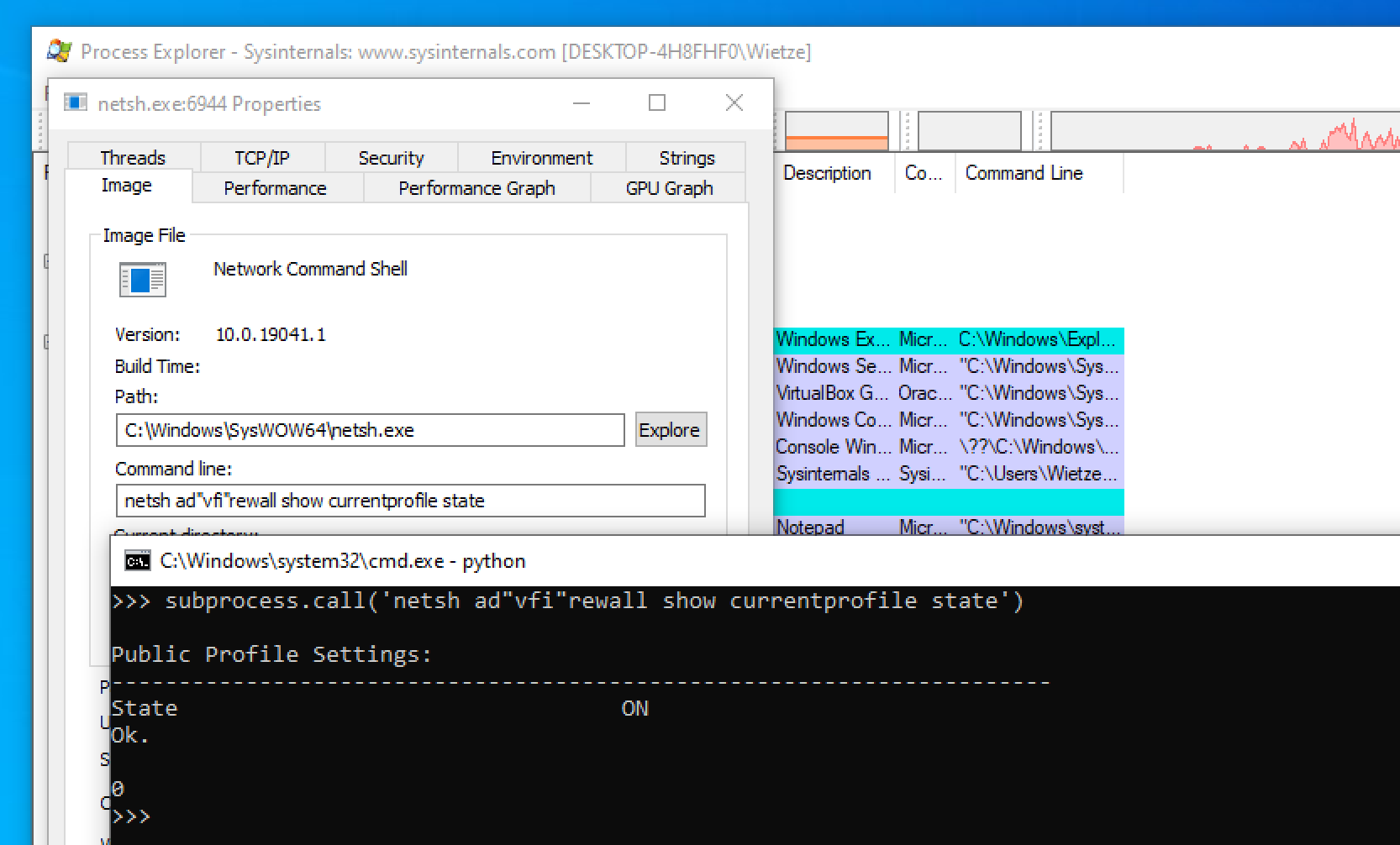
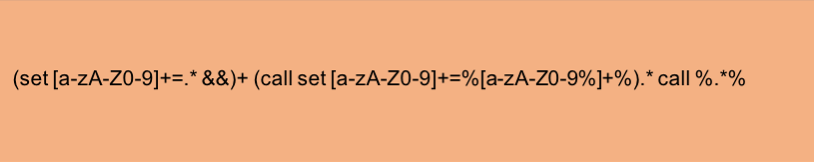
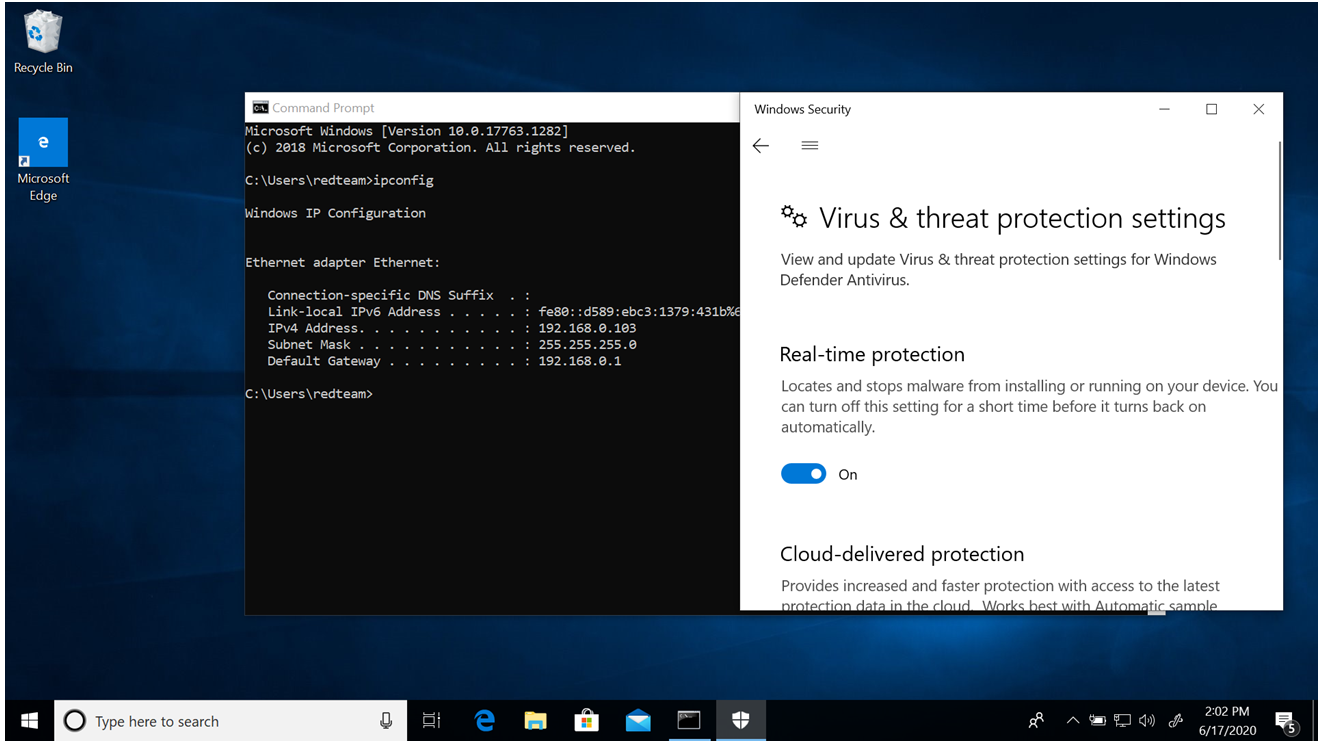
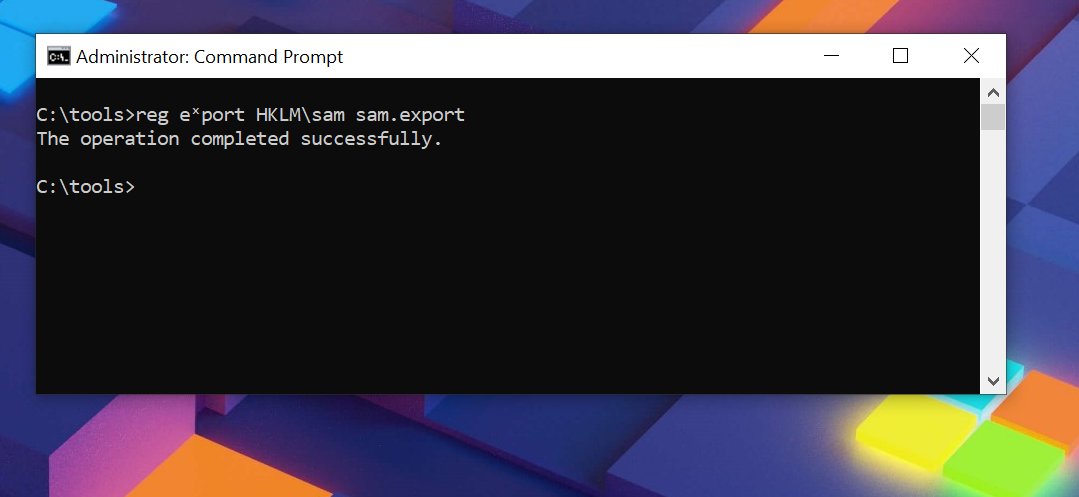
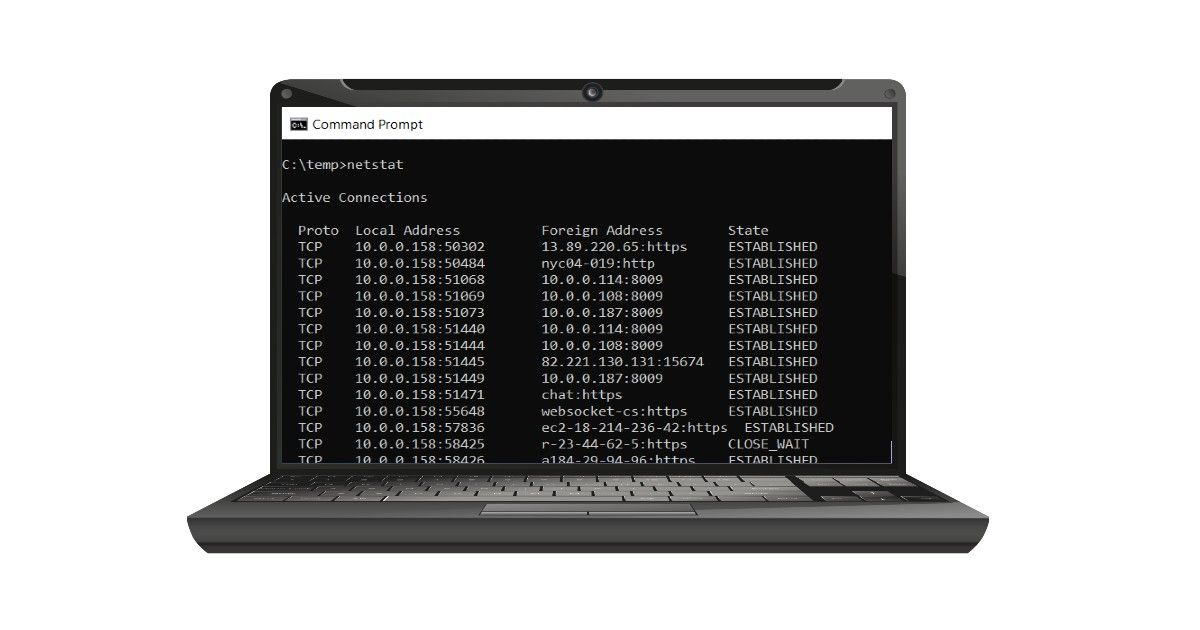
Many Windows applications have multiple ways in which the same command line can be expressed, usually for compatibility or ease-of-use reasons. As a result, command-line arguments are implemented inconsistently making detecting specific commands harder due to the number of variations. This post shows how more than 40 often-used, built-in Windows applications are vulnerable to forms of command-line obfuscation, and presents a tool for analysing other executables.
CB16] Invoke-Obfuscation: PowerShell obFUsk8tion Techniques & How
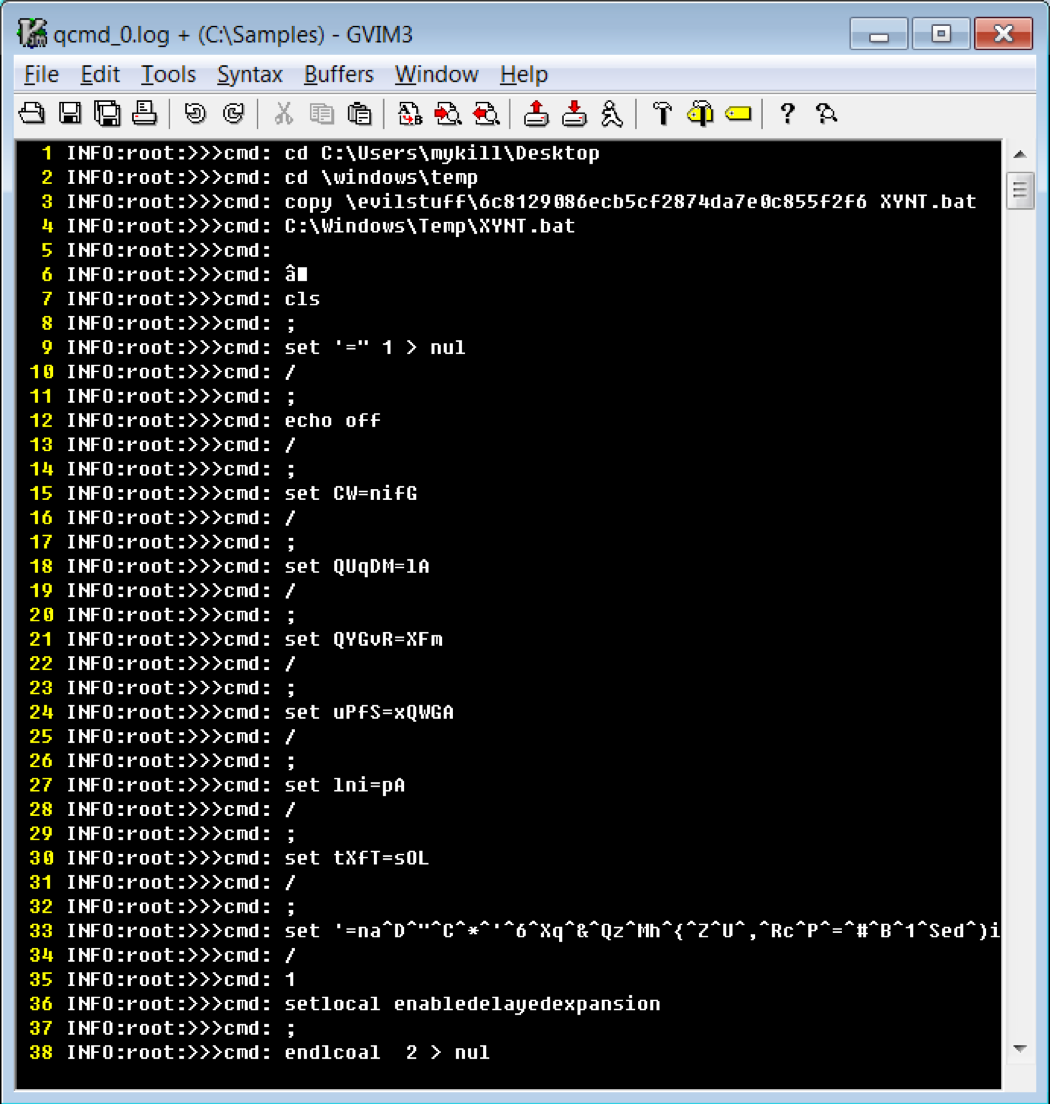
Cmd and Conquer: De-DOSfuscation with flare-qdb - REAL security
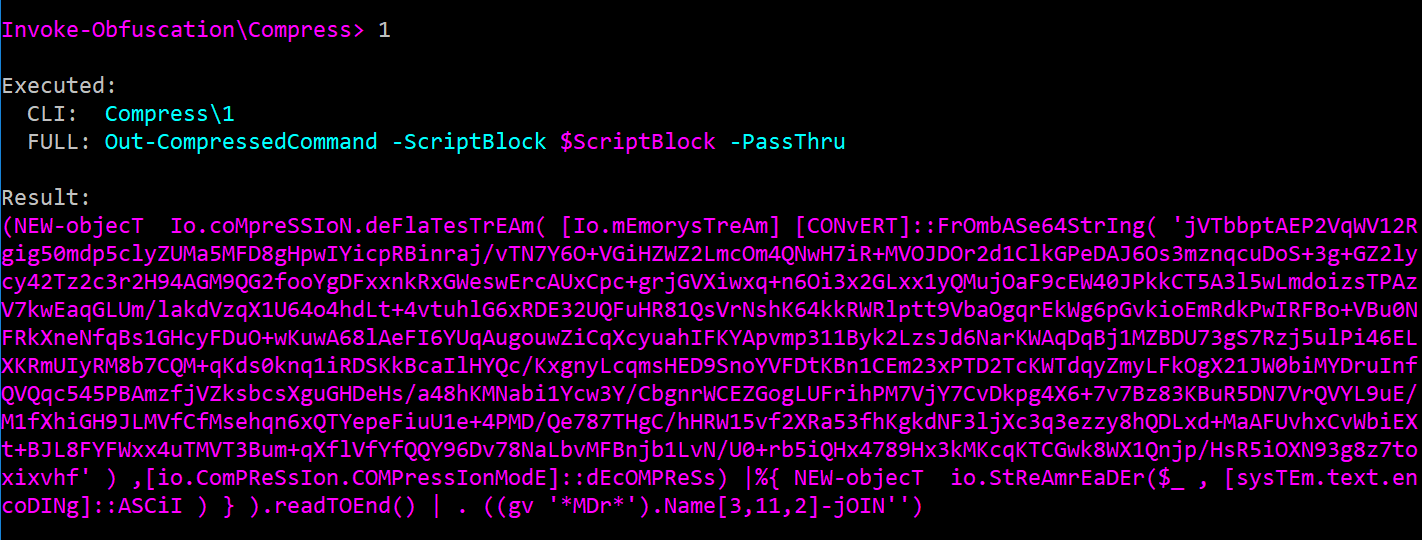
The Invoke-Obfuscation Usage Guide :: Part 2 — Daniel Bohannon
Command-Line Obfuscation
Obfuscated Command Line Detection Using Machine Learning

Exploring Windows Command-Line Obfuscation
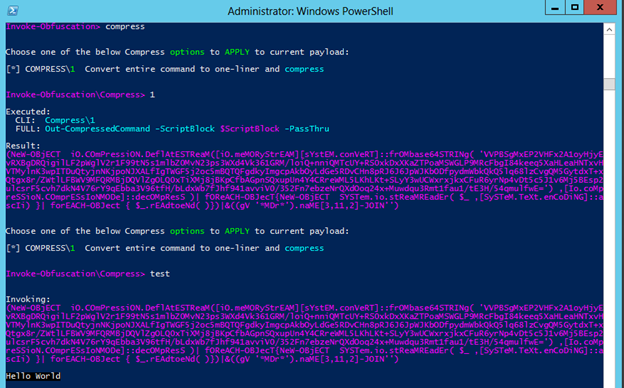
Invoke-Obfuscation — Hiding Payloads To Avoid Detection
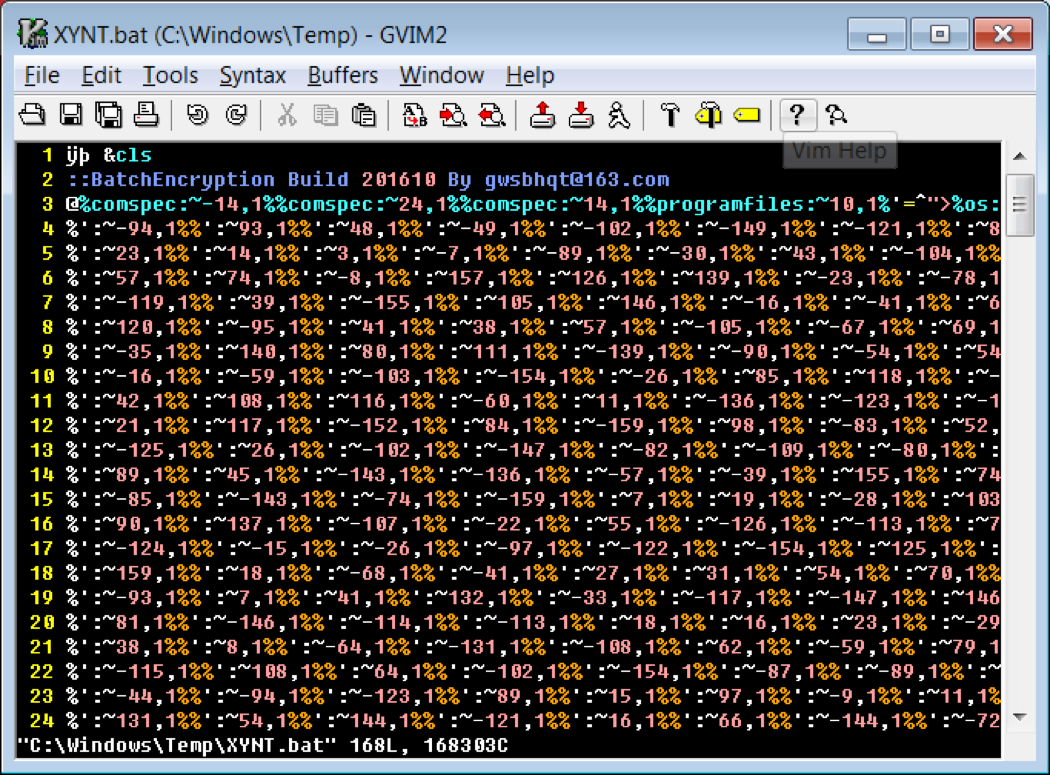
Cmd and Conquer: De-DOSfuscation with flare-qdb

hacking-material-books/obfuscation/simple_obfuscation.md at master
Evading Windows Defender using obfuscation techniques

CB16] Invoke-Obfuscation: PowerShell obFUsk8tion Techniques & How

De-obfuscate/Decode Files or Information - Red Team Notes 2.0

Commandline Obfusaction - Red Team Notes
Florian Roth on X: Sigma rule to detect suspicious Unicode
Recomendado para você
-
 What is the difference between CMD and Command prompt in windows? - Super User31 março 2025
What is the difference between CMD and Command prompt in windows? - Super User31 março 2025 -
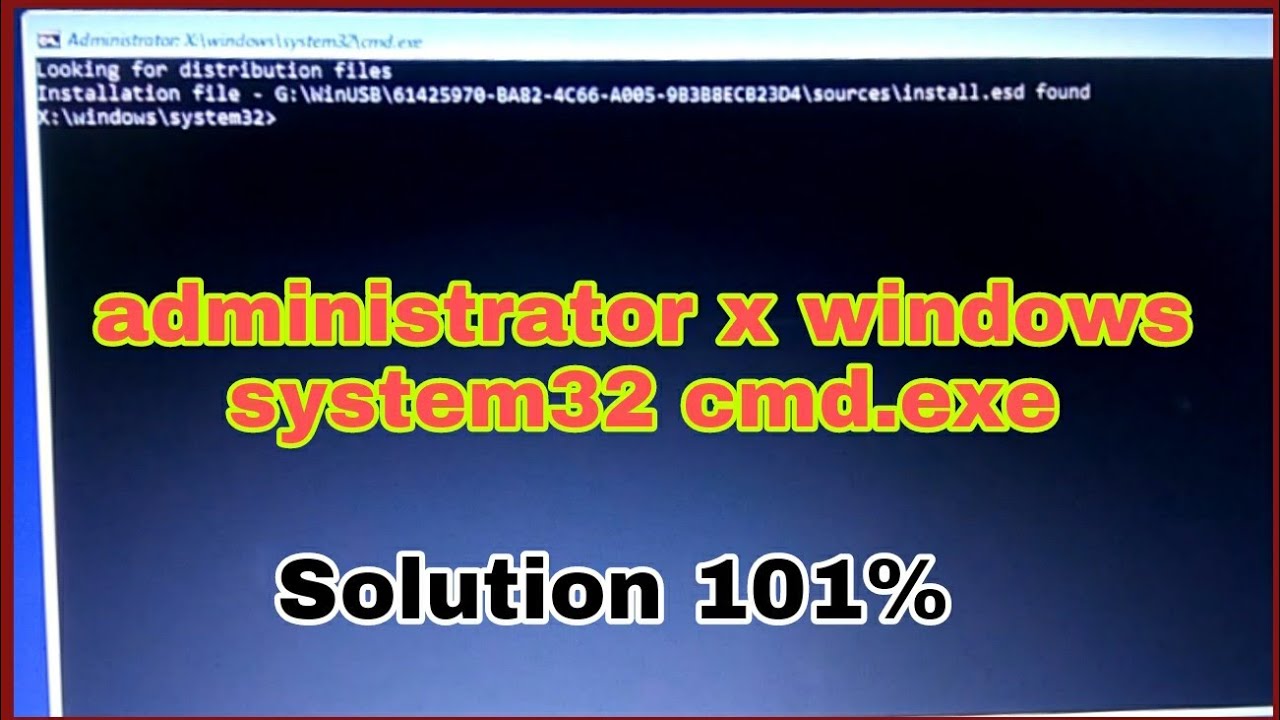 administrator x windows system32 cmd.exe, How to repair administrator x windows, Hiking Tech31 março 2025
administrator x windows system32 cmd.exe, How to repair administrator x windows, Hiking Tech31 março 2025 -
 cmd Commands: 100+ Best Best Command Prompt Commands List You Should Try - MySmartPrice31 março 2025
cmd Commands: 100+ Best Best Command Prompt Commands List You Should Try - MySmartPrice31 março 2025 -
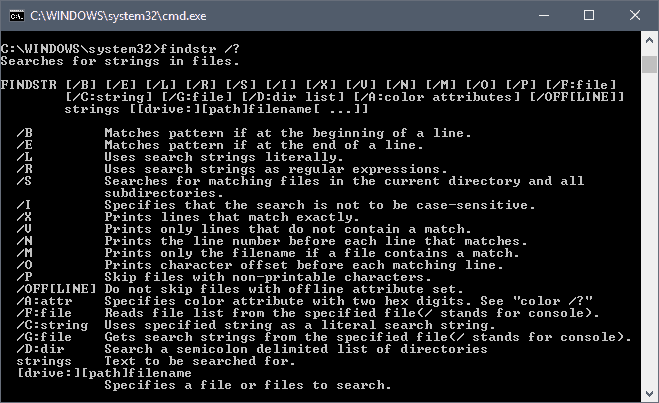 findstr review: Handy Windows tool for command searches for text strings - gHacks Tech News31 março 2025
findstr review: Handy Windows tool for command searches for text strings - gHacks Tech News31 março 2025 -
:max_bytes(150000):strip_icc()/windows-7-cmd-commands-5814df755f9b581c0baede29-94af281c8d1f455f9eee80d9e8d3fef8.jpg) List of Windows 7 Command Prompt Commands31 março 2025
List of Windows 7 Command Prompt Commands31 março 2025 -
 How to Use the Windows Command Line (DOS)31 março 2025
How to Use the Windows Command Line (DOS)31 março 2025 -
 Configuring the Command Prompt Window31 março 2025
Configuring the Command Prompt Window31 março 2025 -
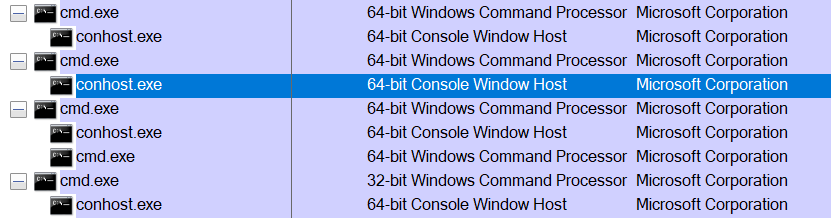 The Windows Process Journey — conhost.exe (Console Window Host), by Shlomi Boutnaru, Ph.D.31 março 2025
The Windows Process Journey — conhost.exe (Console Window Host), by Shlomi Boutnaru, Ph.D.31 março 2025 -
 How to improve the readability of Windows console windows - gHacks Tech News31 março 2025
How to improve the readability of Windows console windows - gHacks Tech News31 março 2025 -
 This window titled “C:/WINDOWS/system32/cmd.exe” randomly appears on my computer sometimes. Does anyone know what this could be? : r/computers31 março 2025
This window titled “C:/WINDOWS/system32/cmd.exe” randomly appears on my computer sometimes. Does anyone know what this could be? : r/computers31 março 2025
você pode gostar
-
 Ferramenta de chave ajustável grande abertura multifuncional placa do banheiro em movimento mão armadilha universal - AliExpress31 março 2025
Ferramenta de chave ajustável grande abertura multifuncional placa do banheiro em movimento mão armadilha universal - AliExpress31 março 2025 -
 Indicado por digital influencers do MA, 'Joguinho do Tigre' será denunciado à polícia31 março 2025
Indicado por digital influencers do MA, 'Joguinho do Tigre' será denunciado à polícia31 março 2025 -
 The Long-Awaited Return: 'Oshi no Ko' Season 2 Release Date Revealed!31 março 2025
The Long-Awaited Return: 'Oshi no Ko' Season 2 Release Date Revealed!31 março 2025 -
Generic Manga World - Rokudenashi Majutsu Koushi to Akashic31 março 2025
-
Can I play Ghost of Tsushima on Windows 7? - Quora31 março 2025
-
Oath, Slave Harem in the Labyrinth of the Other World Wiki31 março 2025
-
 Rolls Royce Cullinan SUV unveiled31 março 2025
Rolls Royce Cullinan SUV unveiled31 março 2025 -
 Top DAWs of 2023: Outstanding Music Production Platforms for PC and Mac Users - Magnetic Magazine31 março 2025
Top DAWs of 2023: Outstanding Music Production Platforms for PC and Mac Users - Magnetic Magazine31 março 2025 -
 Warzone 2 players “mindblown” by removal of base game modes - Dexerto31 março 2025
Warzone 2 players “mindblown” by removal of base game modes - Dexerto31 março 2025 -
 How to get karma on Reddit31 março 2025
How to get karma on Reddit31 março 2025

