Piggybacking (security) - Wikipedia
Por um escritor misterioso
Last updated 03 abril 2025


What is Piggybacking?, IT Wiki
Social engineering (security) - Wikipedia
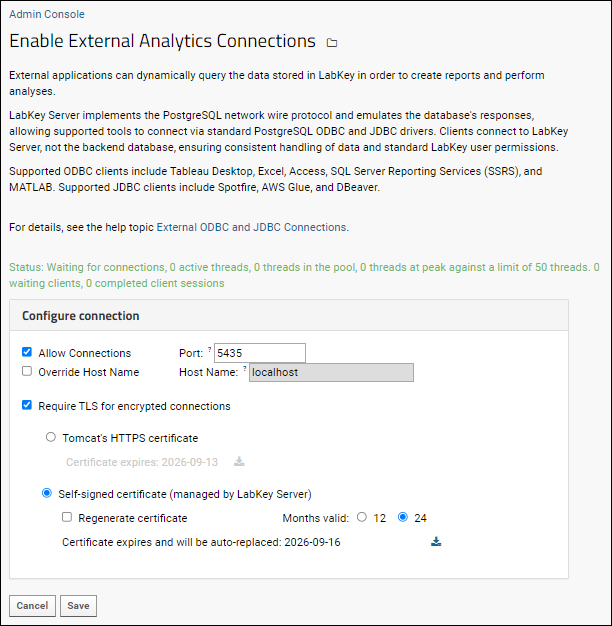
External ODBC and JDBC Connections: /Documentation
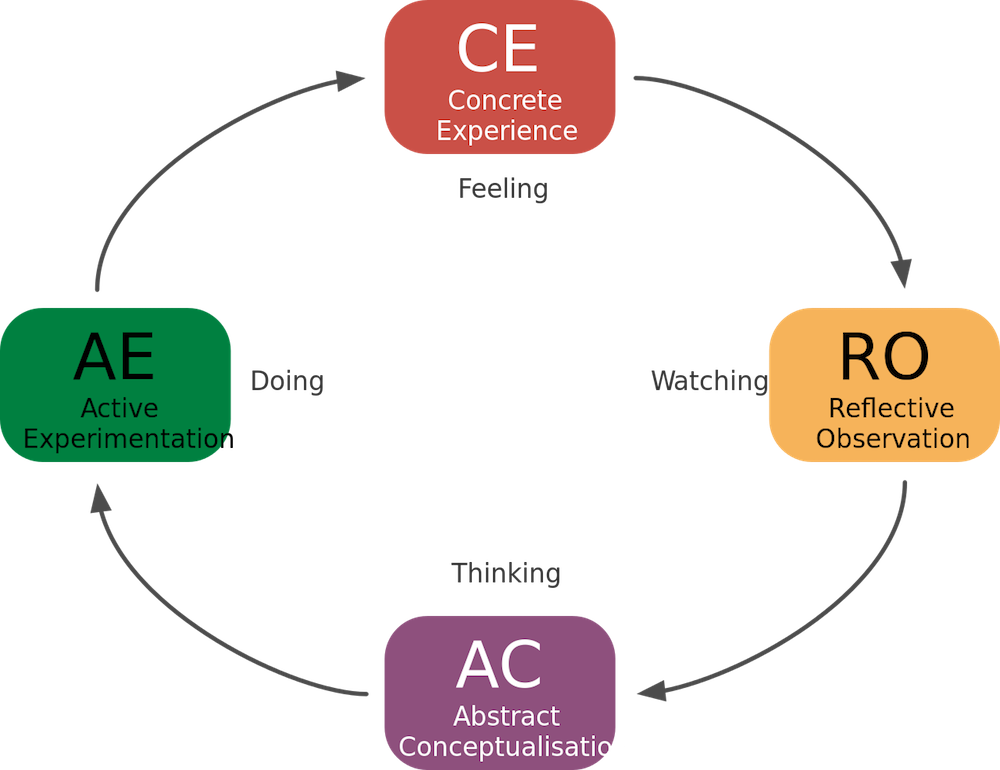
Key Learning Theories Needed for Medical Simulation

Puggyback - Official TF2 Wiki

Piggybacking Attack in the Context of Cybersecurity

Wardriving - Wikipedia

The Piggyback, Stranger Things Wiki

Insight CISO Jason Rader: He Doesn't Have 50 People On His
Little Red Hood, Rare Games Wiki

90% of Cyber Attacks on Organizations Involve Social Engineering
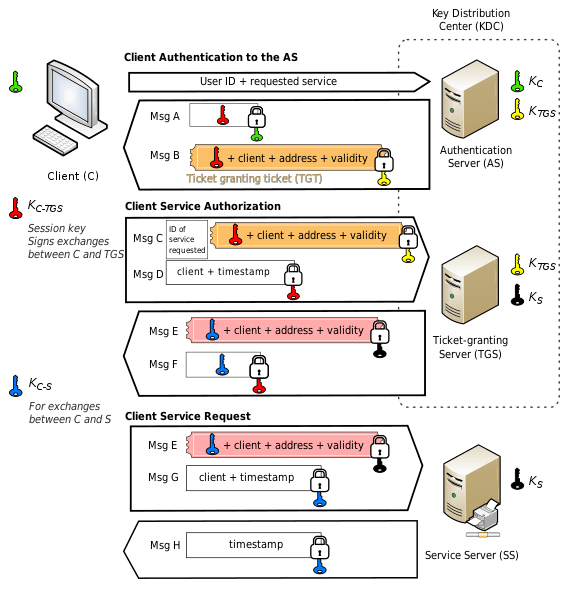
Anomaly detection in certificate-based TGT requests
GitHub - tdr130/android-security-wiki
Recomendado para você
-
 Piggybacking Attack in the Context of Cybersecurity03 abril 2025
Piggybacking Attack in the Context of Cybersecurity03 abril 2025 -
 Piggybacking Definitions, from text book to reality. - Superior Tradelines03 abril 2025
Piggybacking Definitions, from text book to reality. - Superior Tradelines03 abril 2025 -
 Piggyback Songs - Teach Preschool Music03 abril 2025
Piggyback Songs - Teach Preschool Music03 abril 2025 -
Truss - Piggyback Dimensions & Drawings03 abril 2025
-
 Terms Piggyback and Ride along are semantically related or have similar meaning03 abril 2025
Terms Piggyback and Ride along are semantically related or have similar meaning03 abril 2025 -
Piggyback Trailers - Definition of counterfeit. If a Piggyback©® Trailer was not manufactured by us, it's COUNTERFEIT.03 abril 2025
-
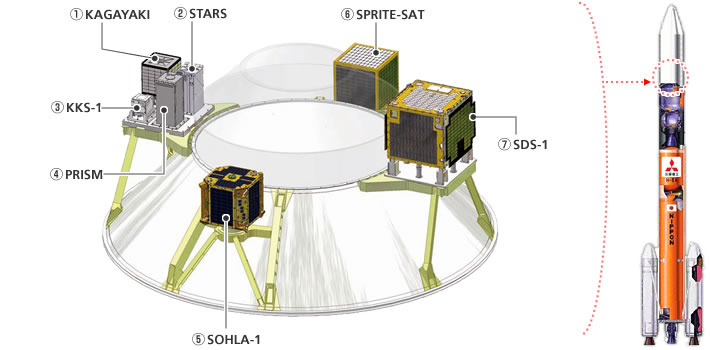 JAXA Piggyback payload03 abril 2025
JAXA Piggyback payload03 abril 2025 -
 72,189 A Woman Without Meaning Stock Photos, High-Res Pictures, and Images - Getty Images03 abril 2025
72,189 A Woman Without Meaning Stock Photos, High-Res Pictures, and Images - Getty Images03 abril 2025 -
 piggyback getgo|大人のための英会話教室|西船橋・荻窪・津田沼03 abril 2025
piggyback getgo|大人のための英会話教室|西船橋・荻窪・津田沼03 abril 2025 -
 piggyback melanie meaning|TikTok Search03 abril 2025
piggyback melanie meaning|TikTok Search03 abril 2025
você pode gostar
-
 Perguntas referentes à análise da crônica de Luis Fernando Verissimo: 1. O texto que acabamos de ler03 abril 2025
Perguntas referentes à análise da crônica de Luis Fernando Verissimo: 1. O texto que acabamos de ler03 abril 2025 -
Ping Pong Equipment for sale in Campo Grande, Brazil, Facebook Marketplace03 abril 2025
-
 Mirror's Edge Gameplay - Chapter 9 - The Shard (Ending and Credits)03 abril 2025
Mirror's Edge Gameplay - Chapter 9 - The Shard (Ending and Credits)03 abril 2025 -
A very poor recreation of Rush's animation03 abril 2025
-
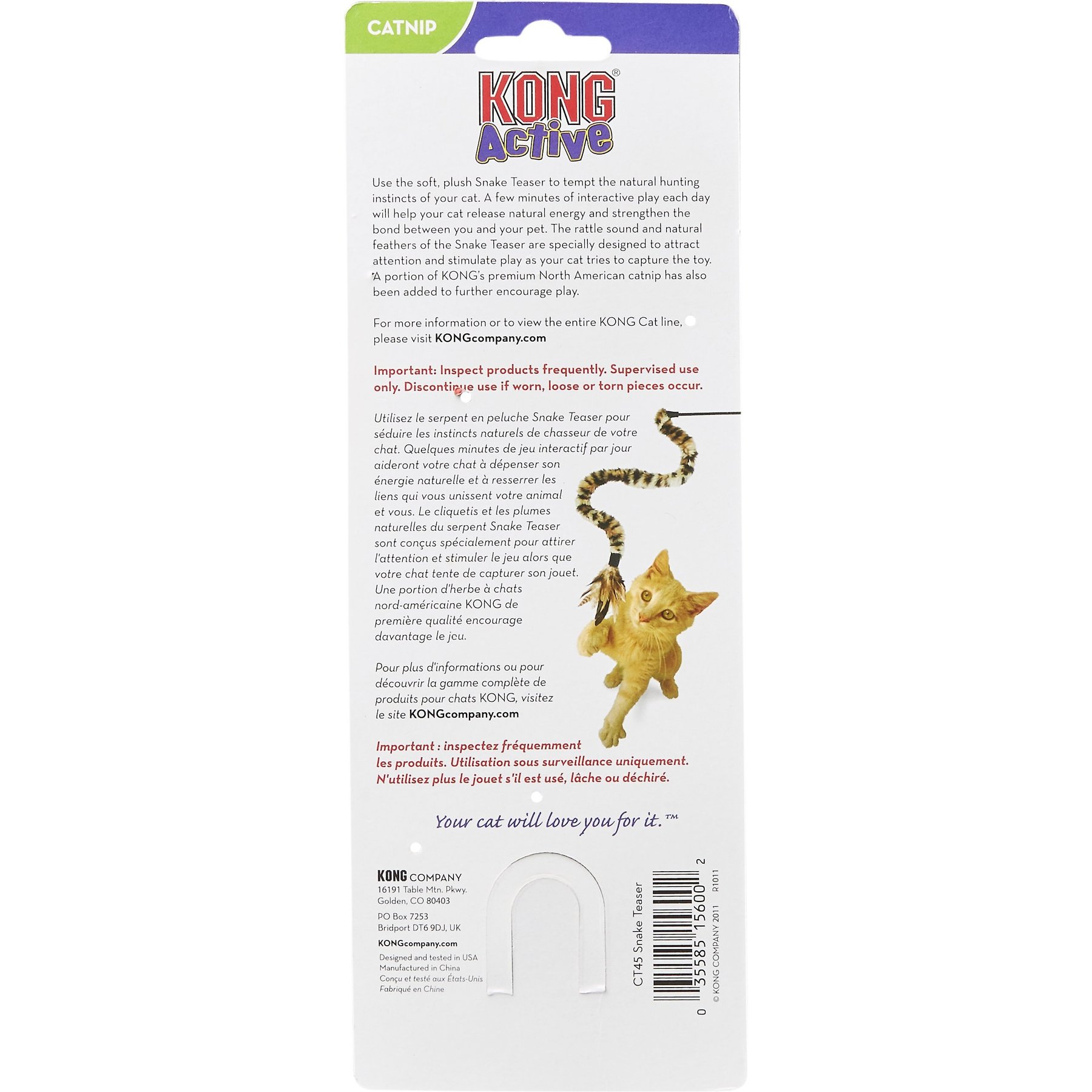 KONG Snake Teaser Cat Toy03 abril 2025
KONG Snake Teaser Cat Toy03 abril 2025 -
 The only new Home Alone movie I will accept : r/funny03 abril 2025
The only new Home Alone movie I will accept : r/funny03 abril 2025 -
 The Honkai Star Rail 1.3 codes are here03 abril 2025
The Honkai Star Rail 1.3 codes are here03 abril 2025 -
 jogo-responda-se-puder-estrela03 abril 2025
jogo-responda-se-puder-estrela03 abril 2025 -
 New Ghost in the Shell Movie Unveils Major Kusanagi Poster!, Anime News03 abril 2025
New Ghost in the Shell Movie Unveils Major Kusanagi Poster!, Anime News03 abril 2025 -
 New League of Legends Prime Gaming Loot Includes RP, Skin, and More03 abril 2025
New League of Legends Prime Gaming Loot Includes RP, Skin, and More03 abril 2025



