Malware analysis Malicious activity
Por um escritor misterioso
Last updated 29 março 2025

Detail procedure of malware analysis
Malware analysis Malicious

Remediation and Malware Detection Overview

Routers Roasting on an Open Firewall: the KV-botnet Investigation

Top 10 Types of Information Security Threats for IT Teams

What is Malware? Definition, Types, Prevention - TechTarget

PROUD-MAL: static analysis-based progressive framework for deep

Malware analysis AIO_4.9.8__ed.rar Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Cybersecurity Search Engine

Malware analysis tt.7z Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation
Lab 6-1 Solutions - Practical Malware Analysis [Book]
GitHub - mesquidar/ForensicsTools: A list of free and open

Malware analysis file Malicious activity
Recomendado para você
-
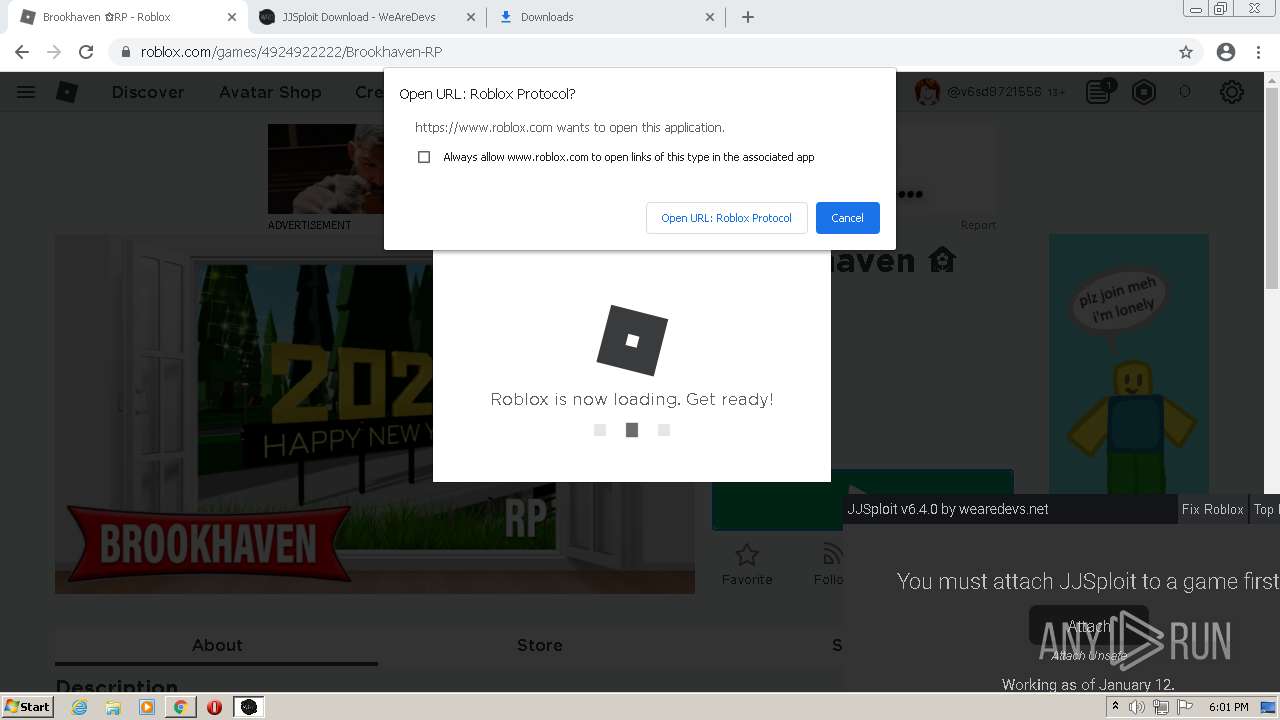
 5 Ways to Play Roblox on a School Chromebook If It's Blocked29 março 2025
5 Ways to Play Roblox on a School Chromebook If It's Blocked29 março 2025 -
 www.roblox.com - site is not usable · Issue #19336 · webcompat/web29 março 2025
www.roblox.com - site is not usable · Issue #19336 · webcompat/web29 março 2025 -
![Play Roblox on Web Browser [Without Downloading] - Alvaro Trigo's Blog](https://alvarotrigo.com/blog/wp-content/uploads/2023/08/roblox-web-browser-share.png) Play Roblox on Web Browser [Without Downloading] - Alvaro Trigo's Blog29 março 2025
Play Roblox on Web Browser [Without Downloading] - Alvaro Trigo's Blog29 março 2025 -
WARNING! ??29 março 2025
-
![UPDATE] Tangled-Web [DEMO] - Spider-Man - Roblox](https://i.ytimg.com/vi/EYxyXVsq2Pw/maxresdefault.jpg) UPDATE] Tangled-Web [DEMO] - Spider-Man - Roblox29 março 2025
UPDATE] Tangled-Web [DEMO] - Spider-Man - Roblox29 março 2025 -
 Roblox Tangled Web Dev Log #1 Starting Stages, Swinging, & Web-Zip29 março 2025
Roblox Tangled Web Dev Log #1 Starting Stages, Swinging, & Web-Zip29 março 2025 -
 Nikalus31 on X: fuck's Profile FuckMeHardDaddyYES's Profile cumonmedaddypls's Profile WHAT IN THE FUCK ROBLOX!? #RobloxDev #roblox #robloxmoderation / X29 março 2025
Nikalus31 on X: fuck's Profile FuckMeHardDaddyYES's Profile cumonmedaddypls's Profile WHAT IN THE FUCK ROBLOX!? #RobloxDev #roblox #robloxmoderation / X29 março 2025 -
 How To Install Roblox From Web Browser On PC - ComputerSluggish29 março 2025
How To Install Roblox From Web Browser On PC - ComputerSluggish29 março 2025 -
 Tangled-Web Information - Bulletin Board - Developer Forum29 março 2025
Tangled-Web Information - Bulletin Board - Developer Forum29 março 2025 -
Catalog - Roblox29 março 2025
você pode gostar
-
 High Card Season 2 Anime Reveals 1st Trailer and January 2024 Debut : r/qooapp29 março 2025
High Card Season 2 Anime Reveals 1st Trailer and January 2024 Debut : r/qooapp29 março 2025 -
 Eu tava jogando GTA San Andreas, e pedi o chat pra me mandar o29 março 2025
Eu tava jogando GTA San Andreas, e pedi o chat pra me mandar o29 março 2025 -
 The Last Thing He Told Me - Apple TV+ Press29 março 2025
The Last Thing He Told Me - Apple TV+ Press29 março 2025 -
 Sweet!~ Anime, Personagens dnd, Animes wallpapers29 março 2025
Sweet!~ Anime, Personagens dnd, Animes wallpapers29 março 2025 -
 Baixar Isekai Meikyuu de Harem wo (Sem Censura) - Download29 março 2025
Baixar Isekai Meikyuu de Harem wo (Sem Censura) - Download29 março 2025 -
 garota de anime com cabelo curto em uma blusa amarela 17206470 Vetor no Vecteezy29 março 2025
garota de anime com cabelo curto em uma blusa amarela 17206470 Vetor no Vecteezy29 março 2025 -
 The Kang Dynasty Explained: One Of The Avengers' Greatest Storylines29 março 2025
The Kang Dynasty Explained: One Of The Avengers' Greatest Storylines29 março 2025 -
 Discord webhook not working (HTTP 403 Error) - Scripting Support29 março 2025
Discord webhook not working (HTTP 403 Error) - Scripting Support29 março 2025 -
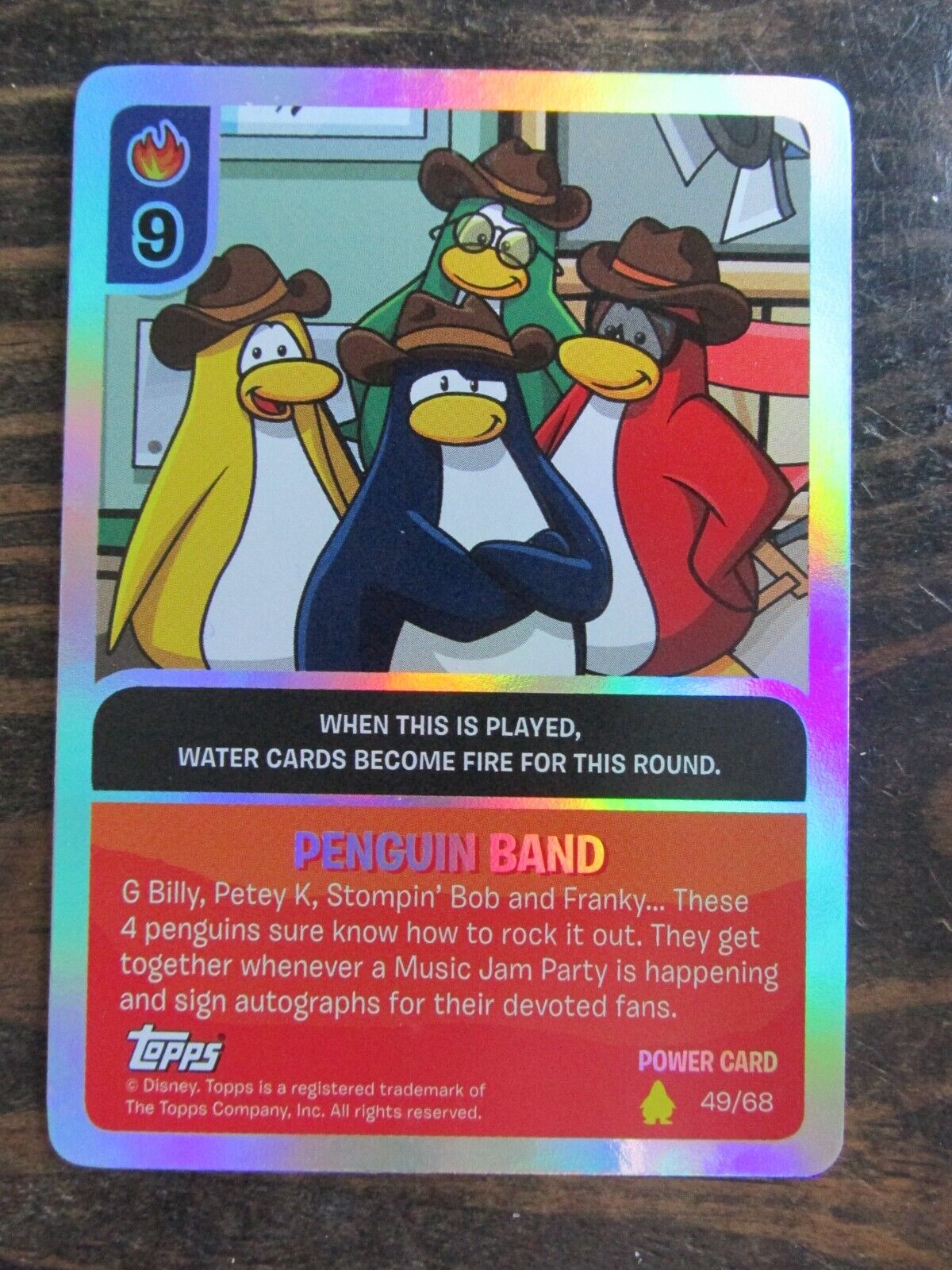 Topps Disney CLUB PENGUIN Power Card Jitsu Card # 9 Penguin Band 49/6829 março 2025
Topps Disney CLUB PENGUIN Power Card Jitsu Card # 9 Penguin Band 49/6829 março 2025 -
Live from PS5 Latest breaking news from PlayStation 5 (US)29 março 2025