Malware analysis Malicious activity
Por um escritor misterioso
Last updated 13 abril 2025

Routers Roasting on an Open Firewall: the KV-botnet Investigation

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Malware Analysis: Steps & Examples - CrowdStrike

Malware analysis tt.7z Malicious activity

Malware analysis CQChallenge5.zip Malicious activity
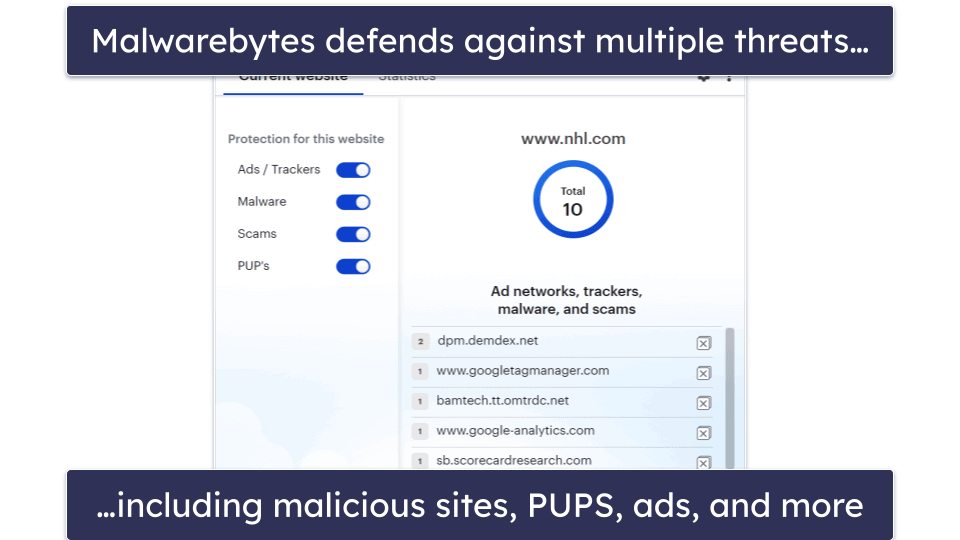
10 Best (REALLY FREE) Antivirus Software for Windows in 2023

Malware Analysis Benefits Incident Response
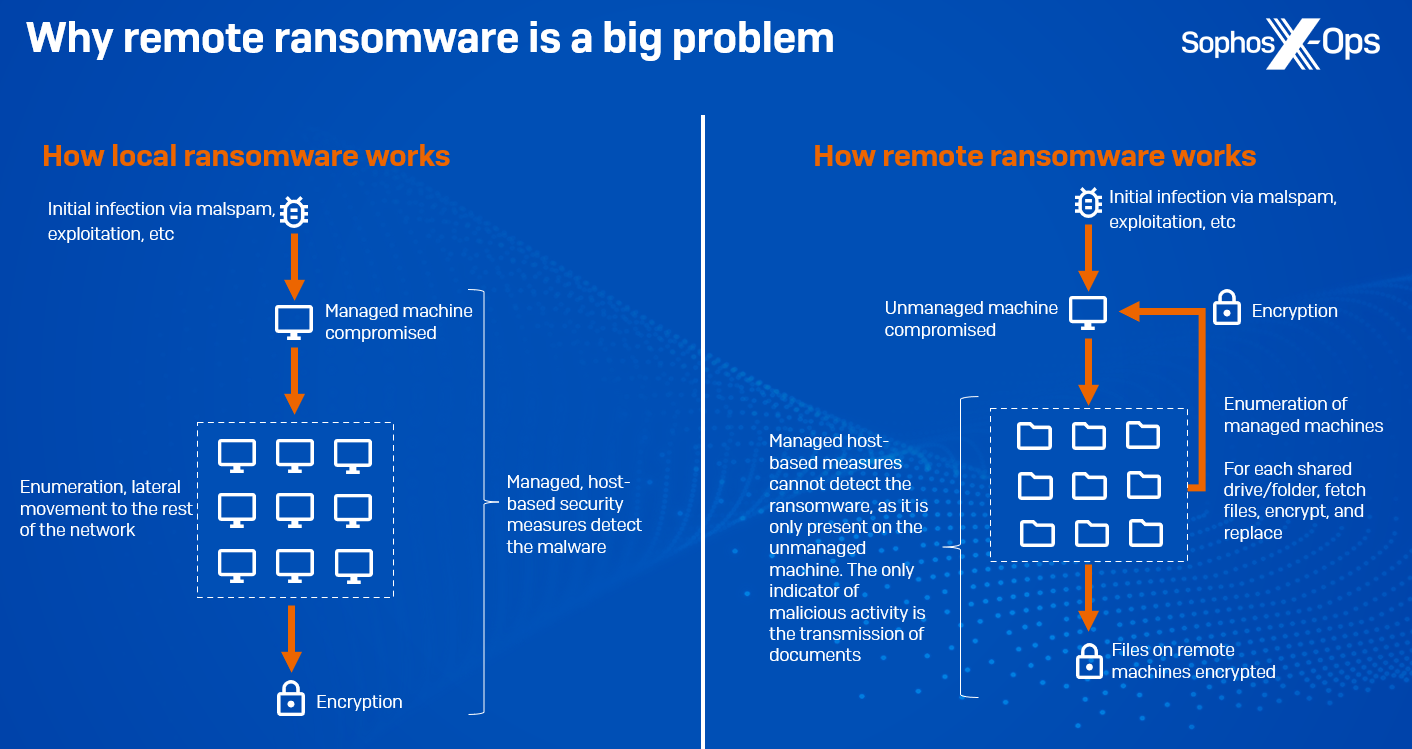
CryptoGuard: An asymmetric approach to the ransomware battle
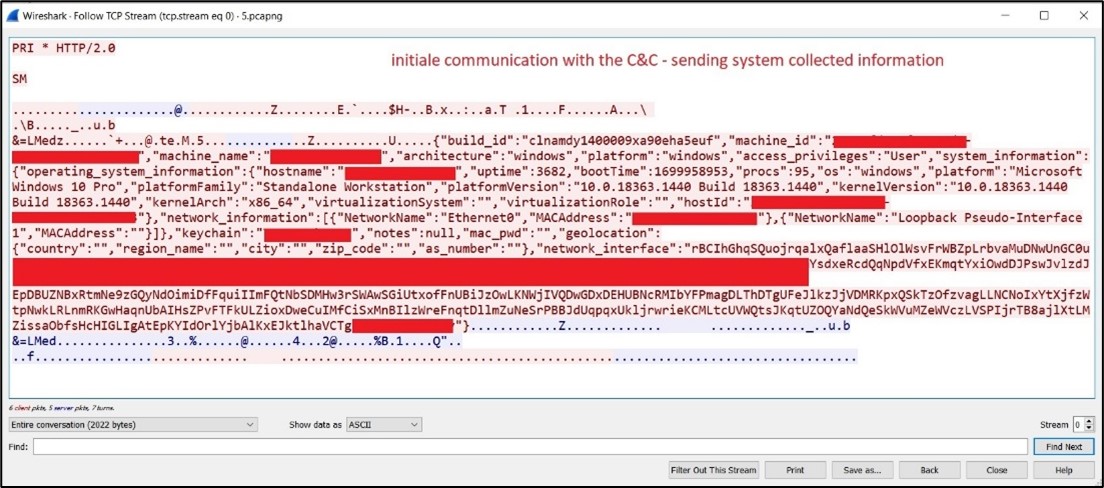
Behind the Scenes: JaskaGO's Coordinated Strike on macOS and Windows

Remediation and Malware Detection Overview

TryHackMe Hacktivities

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Malware analysis

Endpoint Detection and Response, Free - What is EDR Security?

Malware analysis index.html Malicious activity
Recomendado para você
-
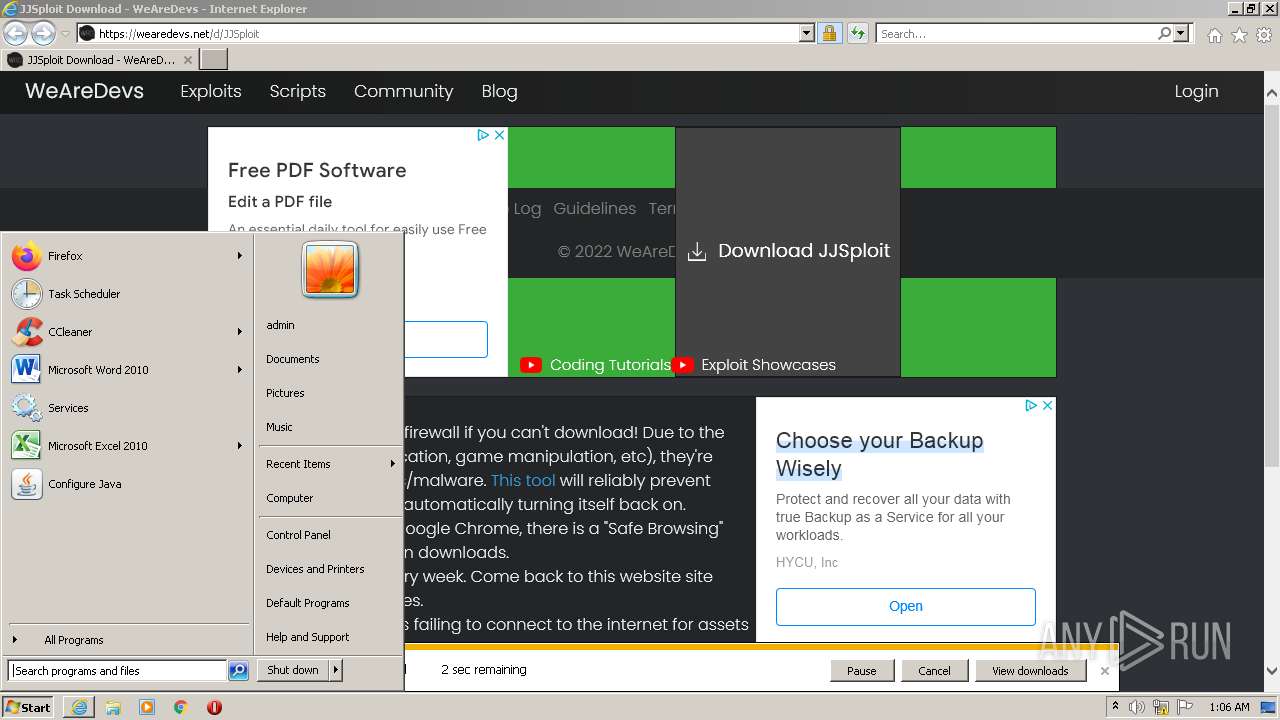
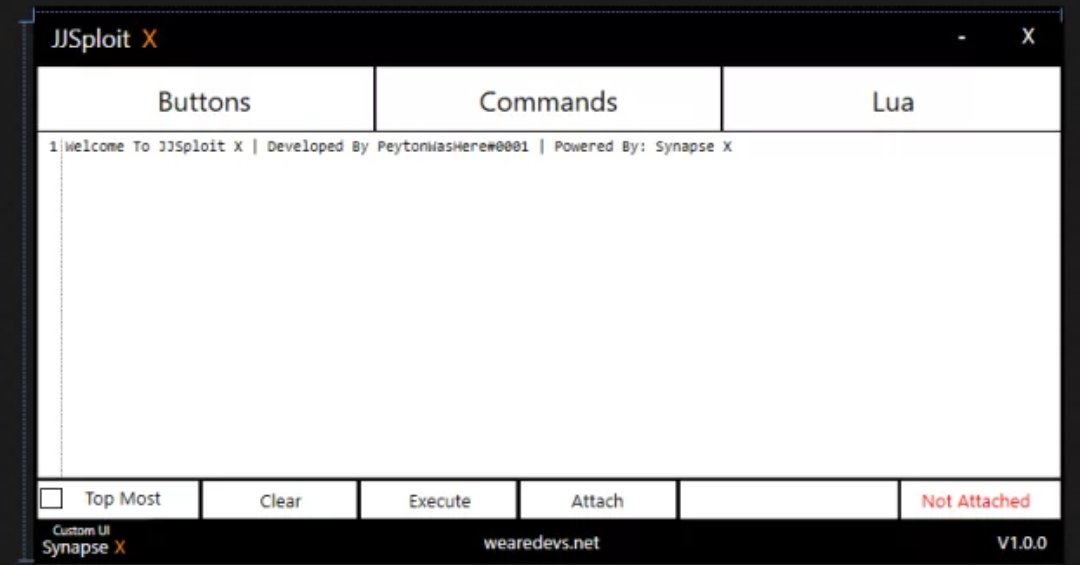 JJSploit - WeAreDevs (@JjSploit) / X13 abril 2025
JJSploit - WeAreDevs (@JjSploit) / X13 abril 2025 -
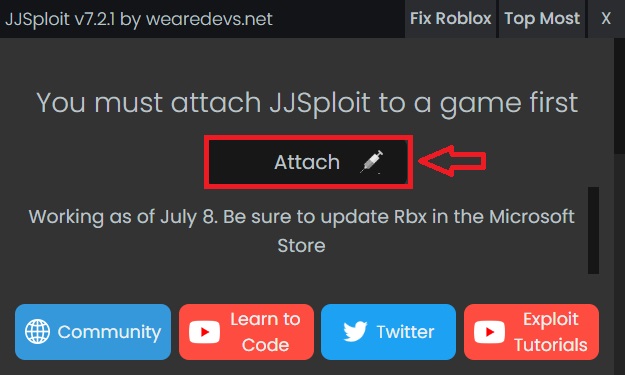 JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay13 abril 2025
JJSploit for Roblox 7.2.1 Download For Windows PC - Softlay13 abril 2025 -
 Jjsploit V4-Www.Wearedevs.Net - Colaboratory13 abril 2025
Jjsploit V4-Www.Wearedevs.Net - Colaboratory13 abril 2025 -
 Wearedevs13 abril 2025
Wearedevs13 abril 2025 -
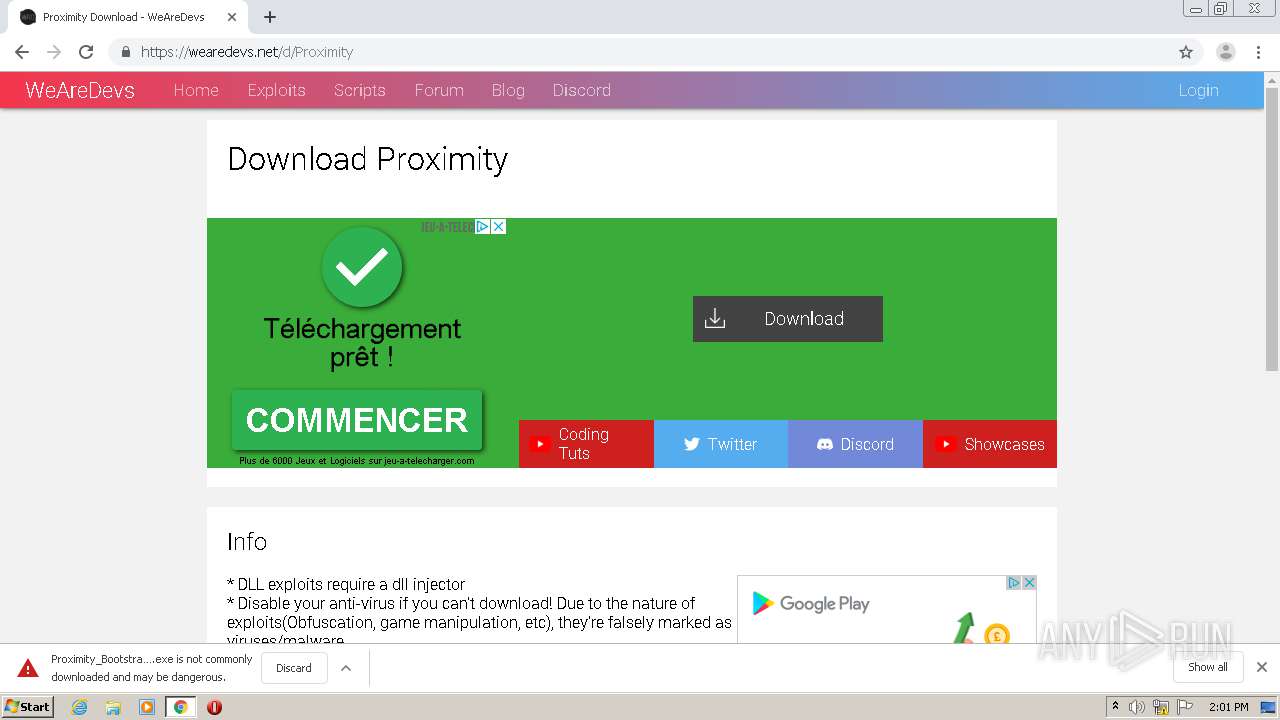 Malware analysis Malicious activity13 abril 2025
Malware analysis Malicious activity13 abril 2025 -
 UnKnoWnCheaTs - Multiplayer Game Hacking and Cheats - View Single13 abril 2025
UnKnoWnCheaTs - Multiplayer Game Hacking and Cheats - View Single13 abril 2025 -
2023 Delta exploits for #videos13 abril 2025
-
 roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment13 abril 2025
roblox #fyo #hack #script #jjsploit #wearedevs Like and Comment13 abril 2025 -
![NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API](https://i.ytimg.com/vi/TIB0v39hQe8/mqdefault.jpg) NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API13 abril 2025
NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API13 abril 2025 -
![NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API FULL LUA SCRIPT SUPPORT WORKING!](https://i.ytimg.com/vi/TIB0v39hQe8/hqdefault.jpg) NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API FULL LUA SCRIPT SUPPORT WORKING!13 abril 2025
NEW] EXTRACT ROBLOX SCRIPT EXECUTOR WORKING 2023 WEAREDEVS API FULL LUA SCRIPT SUPPORT WORKING!13 abril 2025
você pode gostar
-
Steve Void & BEAUZ - Hide And Seek (Lyrics / Lyric Video) ft. Carly Paige - video Dailymotion13 abril 2025
-
 One Piece: Everything we know about God Valley so far - Dexerto13 abril 2025
One Piece: Everything we know about God Valley so far - Dexerto13 abril 2025 -
 Closeup: Deep dive on the new Bryton S800 GPS cycling computer - Bikerumor13 abril 2025
Closeup: Deep dive on the new Bryton S800 GPS cycling computer - Bikerumor13 abril 2025 -
 Pack EW - Rosabella Beauty e Daring Charming13 abril 2025
Pack EW - Rosabella Beauty e Daring Charming13 abril 2025 -
Blue or Red?#happymod #mod #modapp #redorbluepill #Jojoy.io13 abril 2025
-
 Maestra del gambito de dama: la húngara Judit Polgár – DW – 08/12/202013 abril 2025
Maestra del gambito de dama: la húngara Judit Polgár – DW – 08/12/202013 abril 2025 -
 Orlando Health St. Cloud Hospital13 abril 2025
Orlando Health St. Cloud Hospital13 abril 2025 -
 Stream Reaper Sans music Listen to songs, albums, playlists for free on SoundCloud13 abril 2025
Stream Reaper Sans music Listen to songs, albums, playlists for free on SoundCloud13 abril 2025 -
teste pra guildas free fire|Pesquisa do TikTok13 abril 2025
-
 Johnny & Tusk Act 4 max07187 - Illustrations ART street13 abril 2025
Johnny & Tusk Act 4 max07187 - Illustrations ART street13 abril 2025

