Malware analysis Malicious activity
Por um escritor misterioso
Last updated 03 abril 2025

How to Analyze Malware's Network Traffic in A Sandbox

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Endpoint Detection and Response, Free - What is EDR Security?
GitHub - mesquidar/ForensicsTools: A list of free and open forensics analysis tools and other resources

Malware analysis lockysample.bin.zip Malicious activity

Complex 'NKAbuse' Malware Uses Blockchain to Hide on Linux, IoT Machines

What Is Malware Analysis? Definition, Types, Stages, and Best Practices - Spiceworks

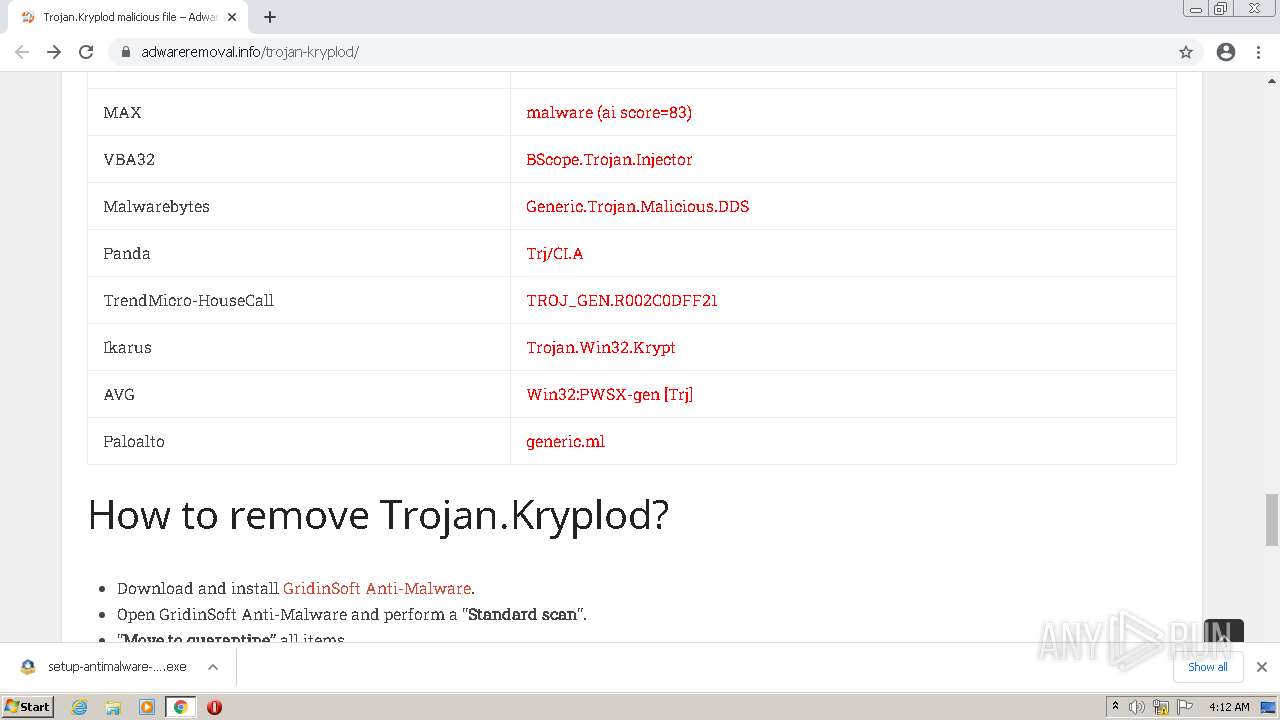
Malware analysis 1071d6d497a10cef44db396c07ccde65 Malicious activity

Cybersecurity Search Engine
Malware analysis Malicious activity

Malware Analysis: Protecting Your Network from Cyber Attacks
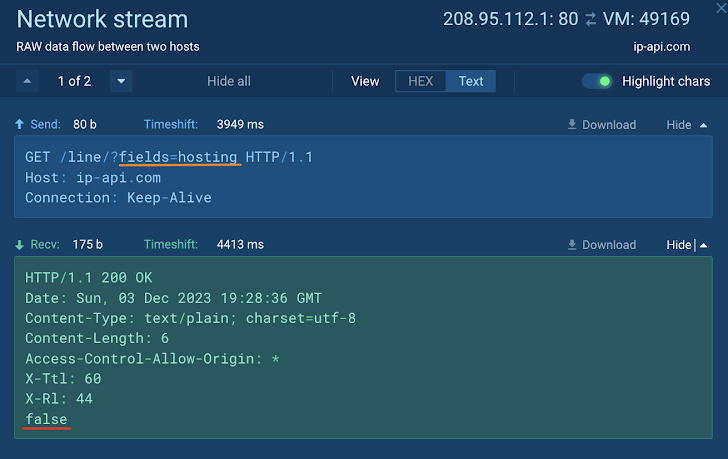
How to Analyze Malware's Network Traffic in A Sandbox
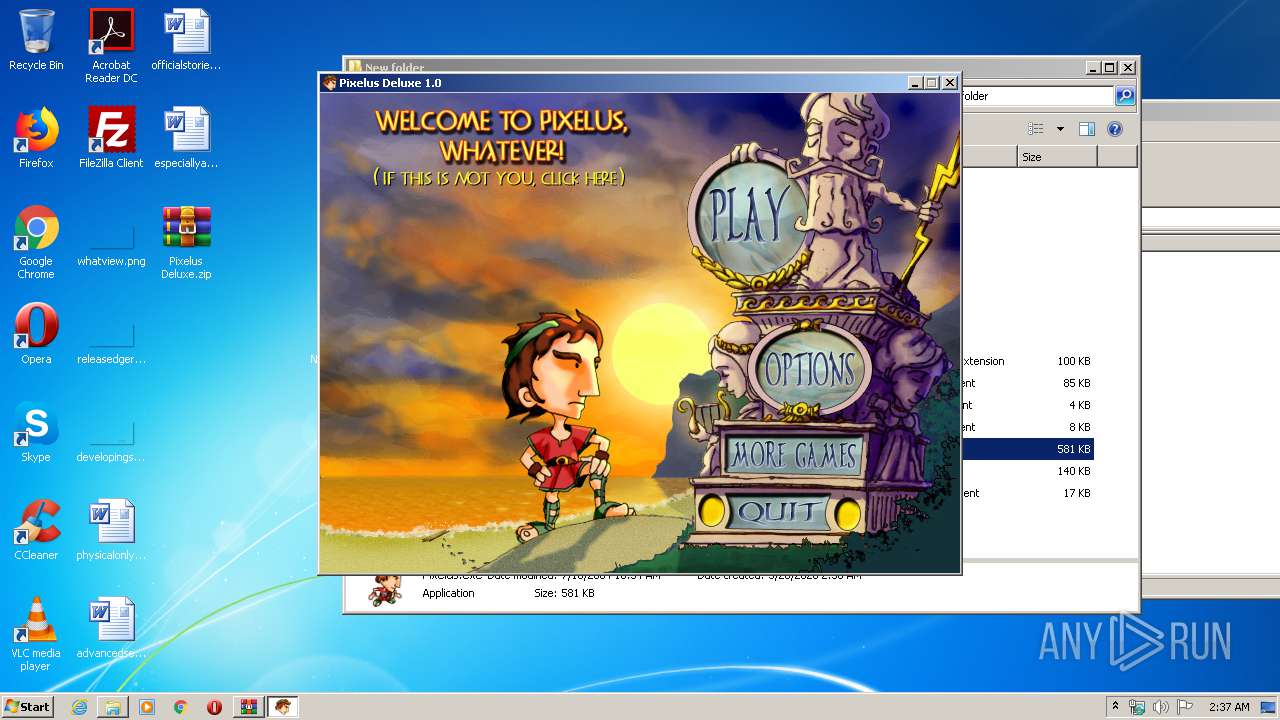
Malware analysis Pixelus Deluxe.zip Malicious activity
Recomendado para você
-
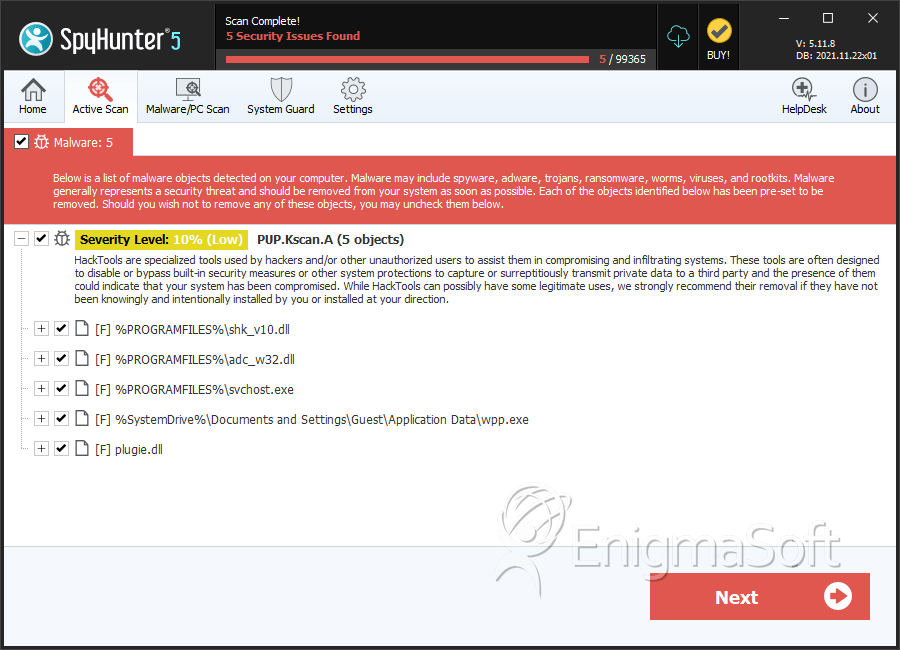 Trojan:Win32/FakeScanti Removal Report03 abril 2025
Trojan:Win32/FakeScanti Removal Report03 abril 2025 -
Fix Ikarus: Trojan.Java.GenericGB flag · Issue #2251 · CCBlueX/Old-LiquidBounce-Issues · GitHub03 abril 2025
-
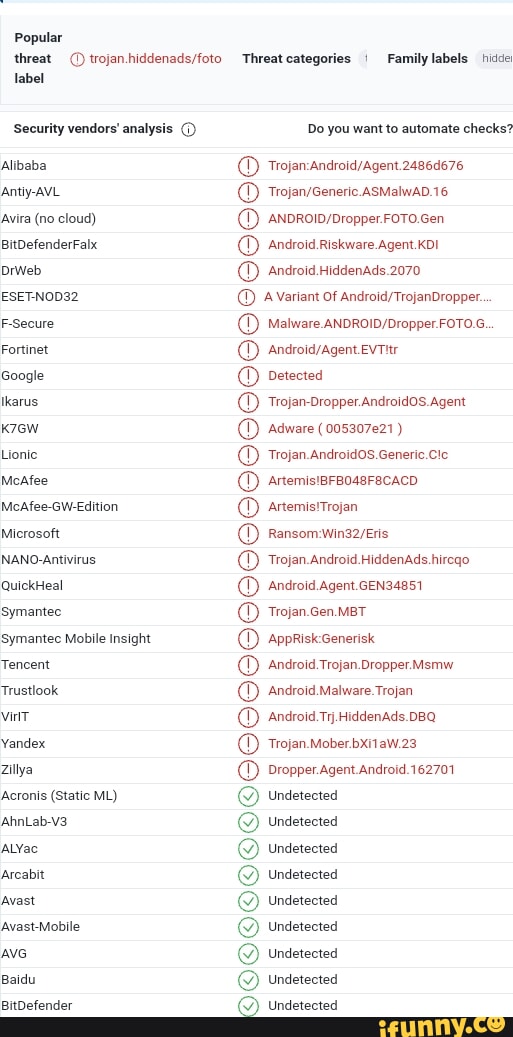 Ikarus memes. Best Collection of funny Ikarus pictures on iFunny Brazil03 abril 2025
Ikarus memes. Best Collection of funny Ikarus pictures on iFunny Brazil03 abril 2025 -
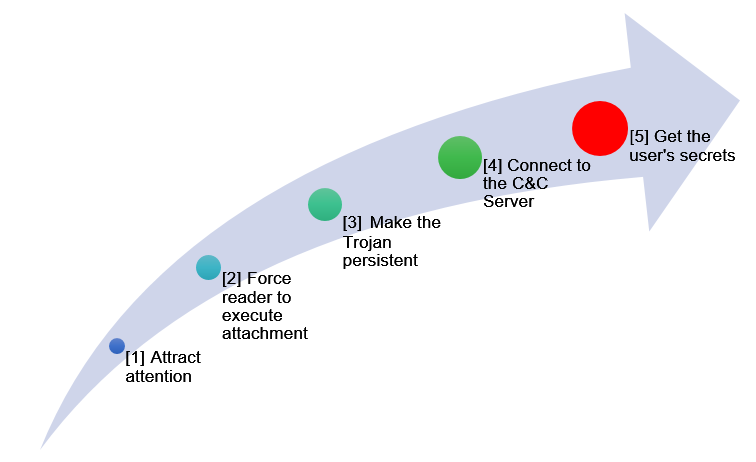 Trojan IT Security Matters03 abril 2025
Trojan IT Security Matters03 abril 2025 -
 Trojan · Issue #230 · pocopico/tinycore-redpill · GitHub03 abril 2025
Trojan · Issue #230 · pocopico/tinycore-redpill · GitHub03 abril 2025 -
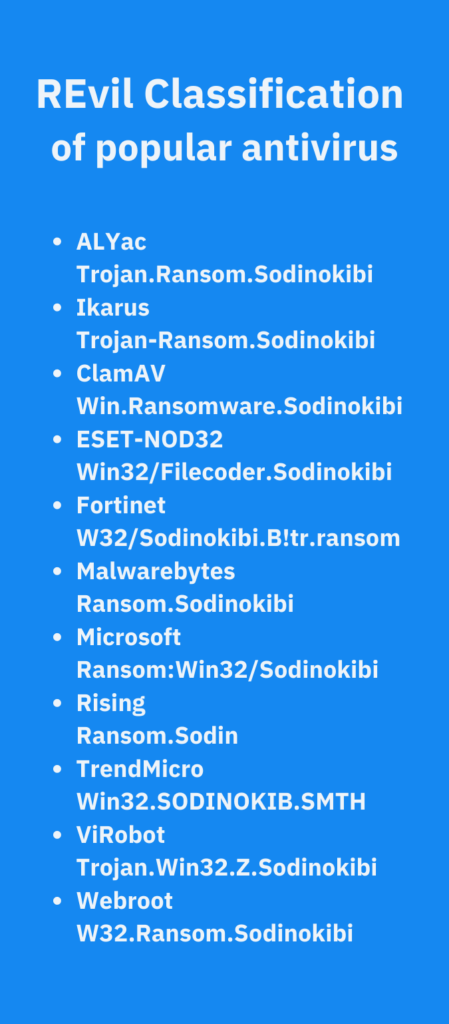 How to Identify & Prevent a Ransomware Attack: REvil Soddinokibi03 abril 2025
How to Identify & Prevent a Ransomware Attack: REvil Soddinokibi03 abril 2025 -
Need Advice - G DATA VS a New Banking Trojan03 abril 2025
-
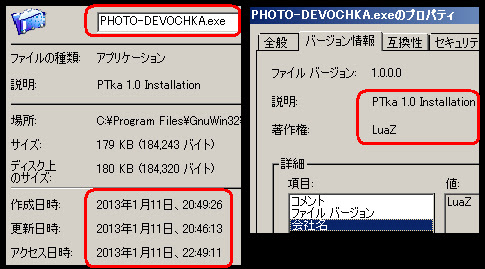 Malware Must Die!: A double hit - PC Trojan W32/VBS Bicololo and Mobile Java Android/Trojan SMS Apps via a hacked Wordpress site03 abril 2025
Malware Must Die!: A double hit - PC Trojan W32/VBS Bicololo and Mobile Java Android/Trojan SMS Apps via a hacked Wordpress site03 abril 2025 -
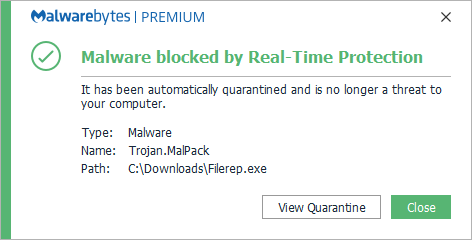 Trojan.Malpack03 abril 2025
Trojan.Malpack03 abril 2025 -
Trojan Virus Found in the Enigma Seven Lives Many Faces (2008) Music CD !!!03 abril 2025
você pode gostar
-
 World Cup 2023: USWNT falls to Sweden in Round of 1603 abril 2025
World Cup 2023: USWNT falls to Sweden in Round of 1603 abril 2025 -
 Katekyo Hitman Reborn Episode 131 - Colaboratory03 abril 2025
Katekyo Hitman Reborn Episode 131 - Colaboratory03 abril 2025 -
 Resultado de imagem para caça palavras coquetel para imprimir03 abril 2025
Resultado de imagem para caça palavras coquetel para imprimir03 abril 2025 -
Comunidade Steam :: Guia :: Sleeping Dogs Definitive Edition03 abril 2025
-
 Xororó expõe o que pensa do marido de Sandy e dá basta em segredo03 abril 2025
Xororó expõe o que pensa do marido de Sandy e dá basta em segredo03 abril 2025 -
Souzones - Eu sempre fiquei nesse dilema de “tenho 1,75m03 abril 2025
-
 PlayStation Store $50 Gift Card03 abril 2025
PlayStation Store $50 Gift Card03 abril 2025 -
Replying to @vegetabadman Reply to @vegetabadman can you use #emulate, emulator website03 abril 2025
-
Wow🤩, it feels like watching anime~~😎😎😎✌ Drama Title: 异人03 abril 2025
-
 Review: building the epic 6000-piece Hogwarts Castle LEGO — Harry Potter Fan Zone03 abril 2025
Review: building the epic 6000-piece Hogwarts Castle LEGO — Harry Potter Fan Zone03 abril 2025



