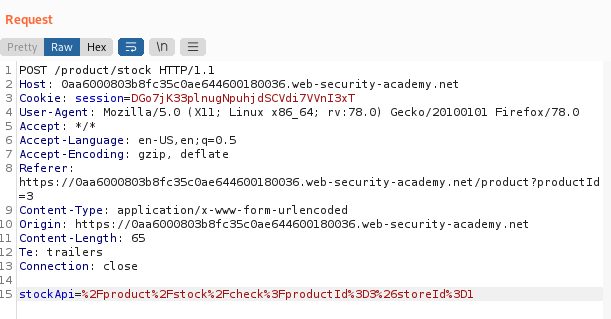
Lab: Blind SSRF with Shellshock exploitation
Por um escritor misterioso
Last updated 03 abril 2025

This site uses analytics software which fetches the URL specified in the Referer header when a product page is loaded. To solve the lab, use this
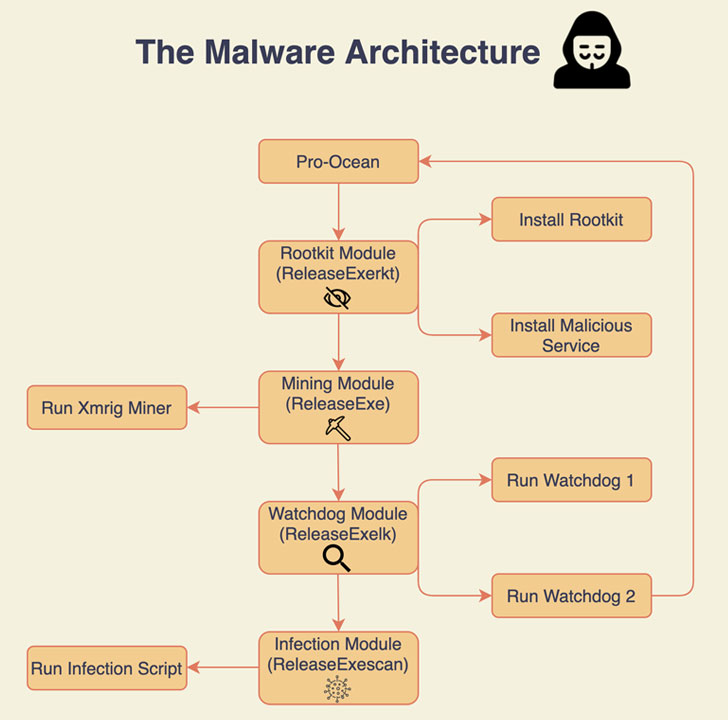
New Cryptojacking Malware Targeting Apache, Oracle, Redis Se
Portswigger Web Security Academy Lab: Blind SSRF with
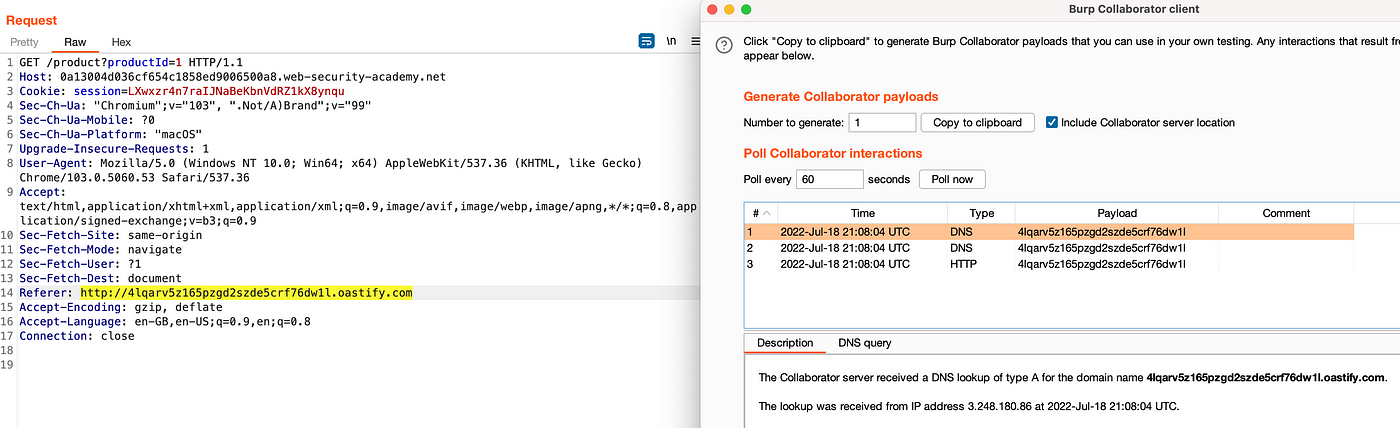
PortSwigger SSRF Labs. Hey all! This write-up is about my…

Blind SSRF with Shellshock exploitation (Video Solution)

Gaining Access through Server-side Request Forgery
Server Side Request Forgery (SSRF) Zafiyeti Nedir? - BGA Cyber
Solving PortSwigger SSRF Labs - Final Part - ::: re:search + re
PayloadsAllTheThings/Server Side Request Forgery/README.md at

TryHackMe Advent of Cyber 2 [2020]

Blind SSRF exploitation ❗️ - Wallarm
Web Security Academy Series Course

Blind SSRF with Shellshock exploitationをやってみた - Shikata Ga Nai
Recomendado para você
-
Shellshock.IO Aimbot & ESP03 abril 2025
-
 Yahoo hack wasn't Shellshock, company claims, The Independent03 abril 2025
Yahoo hack wasn't Shellshock, company claims, The Independent03 abril 2025 -
 Yahoo confirms servers infected — but not by Shellshock03 abril 2025
Yahoo confirms servers infected — but not by Shellshock03 abril 2025 -
 Shellshock Security Flaw - What is it and how it affects everyone - My Blog03 abril 2025
Shellshock Security Flaw - What is it and how it affects everyone - My Blog03 abril 2025 -
 Shellshock Bug May Be Even Bigger Than Heartbleed: What You Need to Know - ABC News03 abril 2025
Shellshock Bug May Be Even Bigger Than Heartbleed: What You Need to Know - ABC News03 abril 2025 -
 BASHLITE Malware Uses ShellShock to Hijack Devices Running BusyBox - SecurityWeek03 abril 2025
BASHLITE Malware Uses ShellShock to Hijack Devices Running BusyBox - SecurityWeek03 abril 2025 -
 Hunting For Shellshock Using Nessus03 abril 2025
Hunting For Shellshock Using Nessus03 abril 2025 -
 Latest Shellshock Attack Uses Bashlite to Target Devices Running BusyBox03 abril 2025
Latest Shellshock Attack Uses Bashlite to Target Devices Running BusyBox03 abril 2025 -
 Hackers 'already using Shellshock bug to attack victims03 abril 2025
Hackers 'already using Shellshock bug to attack victims03 abril 2025 -
 About the Shellshock Vulnerability: The Basics of the “Bash Bug03 abril 2025
About the Shellshock Vulnerability: The Basics of the “Bash Bug03 abril 2025
você pode gostar
-
 FNAF Security Breach by Dreadmon on DeviantArt03 abril 2025
FNAF Security Breach by Dreadmon on DeviantArt03 abril 2025 -
 Detroit: Become Human – Amazingly, It's Quite Good – Henry Vincent03 abril 2025
Detroit: Become Human – Amazingly, It's Quite Good – Henry Vincent03 abril 2025 -
 Rick and Morty Gift Set Shop Online at Build-A-Bear®03 abril 2025
Rick and Morty Gift Set Shop Online at Build-A-Bear®03 abril 2025 -
 Monkey d luffy png Black Friday Casas Bahia03 abril 2025
Monkey d luffy png Black Friday Casas Bahia03 abril 2025 -
 ToraIsMe Anime Fly Race Script03 abril 2025
ToraIsMe Anime Fly Race Script03 abril 2025 -
 O jogo educacional para crianças copia uma imagem de nuvem de desenho animado conectando a planilha de natureza imprimível de ponto03 abril 2025
O jogo educacional para crianças copia uma imagem de nuvem de desenho animado conectando a planilha de natureza imprimível de ponto03 abril 2025 -
 Orphanage on Fire (Another World) Walkthrough Chrono Cross Remaster: Radical Dreamers|Game803 abril 2025
Orphanage on Fire (Another World) Walkthrough Chrono Cross Remaster: Radical Dreamers|Game803 abril 2025 -
 Mega Menacing Mutant Mollusk Munching Camp @ Lac Boeuf II — Baton Rouge Gallery03 abril 2025
Mega Menacing Mutant Mollusk Munching Camp @ Lac Boeuf II — Baton Rouge Gallery03 abril 2025 -
 Classroom of the Elite' 3rd Season Anime Reveals Latest Promo03 abril 2025
Classroom of the Elite' 3rd Season Anime Reveals Latest Promo03 abril 2025 -
 By Kamii em 2023 Kakashi anbu, Kakashi, Ilustrações retro03 abril 2025
By Kamii em 2023 Kakashi anbu, Kakashi, Ilustrações retro03 abril 2025
